Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering APT Group Masqueraded as Indonesia’s Foreign Ministries in Emails...
Month: June 2023
Advanced Threat Hunting: Cutting-Edge Techniques for Seasoned Cyber Defenders – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
DOJ’s New Cyber Unit to Focus on Nation-State Cybercrimes – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Standards, Regulations & Compliance US Justice Department Aims to Accelerate Disruption...
State Fines Kaiser Permanente $450K for PHI Mailing Blunder – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , HIPAA/HITECH , Privacy System Update Error Triggered the Mailing of 337,747 Letters to Old Addresses Marianne...
Unveiling the Unseen: Identifying Data Exfiltration with Machine Learning – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023The Hacker NewsNetwork Security / Machine Learning Why Data Exfiltration Detection is Paramount? The world is witnessing an exponential...
Critical Flaw Found in WordPress Plugin for WooCommerce Used by 30,000 Websites – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananWebsite Security / WordPress A critical security flaw has been disclosed in the WordPress “Abandoned Cart Lite for...
Zero-Day Alert: Apple Releases Patches for Actively Exploited Flaws in iOS, macOS, and Safari – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananVulnerability / Endpoint Security Apple on Wednesday released a slew of updates for iOS, iPadOS, macOS, watchOS, and...
High Risk Users and Where to Fin Them by Elevate Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Apple Patches iOS Flaws Used in Kaspersky ‘Operation Triangulation’ – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Apple has rolled out a major security-themed iOS update to fix remote code execution vulnerabilities that have already been exploited...
CISOs’ New Stressors Brought on by Digitalization: Report – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Whether cloud migration is a cause or effect of digitalization, it is nevertheless a major part of the journey currently...
Cooperation or Competition? China’s Security Industry Sees the US, Not AI, as the Bigger Threat – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press After years of breakneck growth, China’s security and surveillance industry is now focused on shoring up its vulnerabilities to the...
Critical WordPress Plugin Vulnerabilities Impact Thousands of Sites – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Web application security firm Defiant warns of critical-severity authentication bypass vulnerabilities in two WordPress plugins with tens of thousands of...
Kaspersky Dissects Spyware Used in iOS Zero-Click Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Russian anti-malware vendor Kaspersky has analyzed the spyware implant deployed as part of recent zero-click iMessage attack that targeted iOS-powered...
Enphase Ignores CISA Request to Fix Remotely Exploitable Flaws – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Cybersecurity and Infrastructure Security Agency (CISA) this week issued advisories detailing two unpatched vulnerabilities in Enphase products. An...
CISO Conversations: Three Leading CISOs From the Payment Industry – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend SecurityWeek talks to leading Chief Information Security Officers in the payments industry about their role and experience as CISOs. In...
DOJ Launches Cyber Unit to Prosecute Nation-State Threat Actors – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The United States Department of Justice (DOJ) has created a new litigating section to increase its ability to disrupt and...
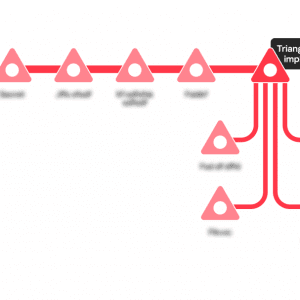
Analyzing the TriangleDB implant used in Operation Triangulation – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Kaspersky provided more details about Operation Triangulation, including the exploitation chain and the implant used by the threat actors. Kaspersky...
Russia-linked APT28 hacked Roundcube email servers of Ukrainian entities – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked APT28 group hacked into Roundcube email servers belonging to multiple Ukrainian organizations. A joint investigation conducted by Ukraine’s Computer...
New Condi DDoS botnet targets TP-Link Wi-Fi routers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers discovered a new strain of malware called Condi that targets TP-Link Archer AX21 (AX1800) Wi-Fi routers. Fortinet FortiGuard Labs Researchers discovered a...
BrandPost: Reducing Cyber Risks by Upskilling Your Security Talent – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | CISOs today face an expanding attack surface, increasingly threats, and a cybersecurity skills gap. An integrated and automated approach to...
BrandPost: Taking a Centralized Approach to Cloud Security – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | CISOs today face an expanding attack surface, increasingly threats, and a cybersecurity skills gap. An integrated and automated approach to...
Why you should review the security of your MSSQL servers – Source: www.csoonline.com
Source: www.csoonline.com – Author: MS SQL Server is by far the most common DBMS that attackers target, probably due to its tight integration with Windows. Brute-force...
Ransomware attacks pose communications dilemmas for local governments – Source: www.csoonline.com
Source: www.csoonline.com – Author: Experts say it’s crucial that local governments communicate with the public following a ransomware attack but must walk a fine line between...
BrandPost: Reducing waste in value generation centers with OT security – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | Cybersecurity has a communication problem. It’s understood that action is needed to improve the global security posture, but ineffective communication...
Baffle launches new user interface to simplify application data security – Source: www.csoonline.com
Source: www.csoonline.com – Author: Baffle Manager 2.0 adds REST APIs, secrets store, certificate store, and SSO to fully automate data protection over SaaS workflows.s iStock Data...
This is what OpenAI’s AI app store will look like… – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: OpenAI, the company behind ChatGPT (the chatbot that has dazzled the internet), wants to create a marketplace that will...
News Alert: NowSecure Achieves SOC 2 Type 2 certification for 4th consecutive year – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Chicago, Ill., June 21, 2023 – NowSecure, the recognized experts in mobile security and privacy, announced today that it has completed...
News Alert: IRONSCALES beta-launches a new generative AI tool to improve email security – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Atlanta, Ga. June 20, 2023 – IRONSCALES, the leading enterprise cloud email security platform protecting more than 10,000 global organizations worldwide,...
News Alert: Survey shows vast majority of IT pros consider ‘passwordless’ access a top priority – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Santa Clara, Calif. – June 21, 2023 – Axiad, a leading provider of organization-wide passwordless orchestration, today announced the results of...
GUEST ESSAY: Taking a fresh approach to privileged access management — to curtail abuse – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Ravi Srivatsav To be productive in an interconnected work environment, employees need immediate access to numerous platforms, both on- and...