Source: www.infosecurity-magazine.com – Author: 1 A recent chief information security officers (CISO) survey has shown that supply chain and application programming interfaces (APIs) have emerged as...
Day: June 21, 2023
Security Researchers Uncover New Spyware Implant TriangleDB – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers at Kaspersky have recently uncovered a sophisticated spyware implant called TriangleDB, part of an operation known as Triangulation. According...
#InfosecurityEurope: Compliance Does Not Mean Security, Experts Warn – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Compliance will not give you good security, although effective security can help to support compliance programs, experts argued today. During a...
#InfosecurityEurope: Security Training Failures Impacting Digital Transformation – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Global organizations are still failing to build cybersecurity training into digital transformation initiatives from the very start, imperiling projects and exposing...
#InfosecurityEurope: Transparency and Context Key to Insider Risk Management – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security chiefs must first get employees on board if they want to deliver effective insider risk programs, experts argued today at...
#InfosecurityEurope: One in Three UK&I Workers Susceptible to Phishing – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 More than one in three workers in the UK and Ireland are susceptible to falling for phishing attacks, according to the...
#InfosecurityEurope: Financial Firms to Build Resilience in Face of Growing Cyber-Threats – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cyber-resilience is now a key component of operational resilience for the UK’s financial markets, according to a Bank of England official....
#InfosecurityEurope: Does Pentesting Need a New Service Model? – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Pentesting had been a firm feature in the world of cybersecurity for decades but some argue that the market needs a...
#InfosecurityEurope: Why API Security Could Be the Next Big Thing in Cyber – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 In our modern digital world, application programming interfaces (APIs) have become the backbone of our personal and professional Internet use. They...
#InfosecurityEurope: Security Training Needs to Nudge, Not Nag – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Conventional security awareness training fails to bring lasting changes to user behavior, according to experts in the field. Instead, organizations need...
Chrome and Its Vulnerabilities – Is the Web Browser Safe to Use? – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Like all major applications, Google’s Chrome suffers from vulnerabilities. During 2022, SecurityWeek reported on 456 vulnerabilities (averaging 38 per month),...
Biden Discusses Risks and Promises of Artificial Intelligence With Tech Leaders in San Francisco – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press President Joe Biden convened a group of technology leaders on Tuesday to debate what he called the “risks and enormous...
VMware Confirms Live Exploits Hitting Just-Patched Security Flaw – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Less than two weeks after shipping urgent patches to cover security defects in its Aria Operations for Networks product, VMware...
Researchers Flag Account Takeover Flaw in Microsoft Azure AD OAuth Apps – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Researchers at security startup Descope have discovered a major misconfiguration in Microsoft Azure AD OAuth applications and warned that any...
Russian APT Group Caught Hacking Roundcube Email Servers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine A prolific APT group linked to the Russian government has been caught exploiting security flaws in the open-source Roundcube webmail...
Ensure the security and reliability of your applications at every stage, from development to production, with Uptycs – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Graham Cluley Security News is sponsored this week by the folks at Uptycs. Thanks to the great team there for...
Norton Parent Says Employee Data Stolen in MOVEit Ransomware Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Gen Digital (NASDAQ: GEN), the company behind known cybersecurity brands such as Avast, Avira, AVG, Norton, and LifeLock, has confirmed...
100,000 hacked ChatGPT accounts up for sale on the dark web – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Just a moment… Enable JavaScript and cookies to continue Original Post URL: https://www.bitdefender.com/blog/hotforsecurity/100-000-hacked-chatgpt-accounts-up-for-sale-on-the-dark-web/ Category & Tags: Guest blog,Malware,ChatGPT,OpenAI – Guest...
OT:Icefall: Vulnerabilities Identified in Wago Controllers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Forescout Technologies has disclosed the details of three vulnerabilities impacting operational technology (OT) products from Wago and Schneider Electric. The...
New ‘RDStealer’ Malware Targets RDP Connections – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A state-sponsored espionage campaign is leveraging new custom malware to monitor incoming remote desktop protocol (RDP) connections and infect connecting...
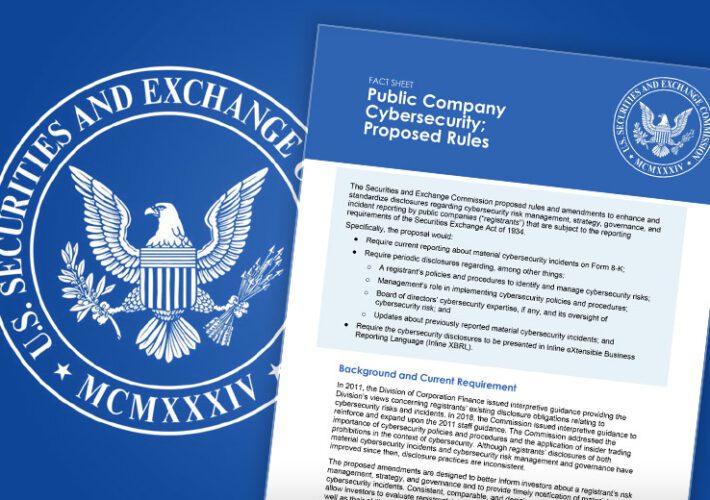
Fulfilling Expected SEC Requirements for Cybersecurity Expertise at Board Level – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The U.S. Securities and Exchange Commission (SEC) is expected to introduce a rule requiring demonstration of cybersecurity expertise at the...
Australian Government Says Its Data Was Stolen in Law Firm Ransomware Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Office of the Australian Information Commissioner (OAIC) says some of its files were stolen in a ransomware attack on...
European Officials Tout Private Sector Collaboration – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management Akshaya Asokan (asokan_akshaya) • June 20, 2023 Image: Shutterstock A top European cybercrime official extoled...
Ukraine Tracks Multiple Spear Phishing Campaigns From Russia – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Russian GRU Hackers Reach for Government Email Inboxes Mihir Bagwe (MihirBagwe) • June 20, 2023 A Ukrainian soldier in...
Groups Urge HHS to Finalize Reproductive Health Data Changes – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , HIPAA/HITECH , Privacy Some Associations Want Certain Privacy Protections Stretched Even Further Marianne Kolbasuk McGee (HealthInfoSec)...
SEC Delays Final Rules on Breach Disclosure, Board Expertise – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Delay Comes Amid Criticism of Rule Requiring 4-Day Disclosure of Material Incidents Michael Novinson (MichaelNovinson) • June 20, 2023 ...
Chinese Hacker Group ‘Flea’ Targets American Ministries with Graphican Backdoor – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 21, 2023Ravie LakshmananCyber Threat / APT Foreign affairs ministries in the Americas have been targeted by a Chinese state-sponsored actor...
New Condi Malware Hijacking TP-Link Wi-Fi Routers for DDoS Botnet Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 21, 2023Ravie LakshmananNetwork Security / Botnet A new malware called Condi has been observed exploiting a security vulnerability in TP-Link...
Alert! Hackers Exploiting Critical Vulnerability in VMware’s Aria Operations Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 21, 2023Ravie LakshmananVulnerability / Network Security VMware has flagged that a recently patched critical command injection vulnerability in Aria Operations...
Why CISOs should be concerned about space-based attacks – Source: www.csoonline.com
Source: www.csoonline.com – Author: Space-based data communications are reliable and useful links for users, but they’re also tempting targets for hackers and other hostile actors. CSOs...