The 3CX Desktop App software has been reportedly compromised via a prior software supply chain breach, with a North Korean actor suspected to be responsible. According...
Day: April 20, 2023
Daggerfly APT Targets African Telecoms Firm With New MgBot Malware
The APT group known as Daggerfly (as well as Evasive Panda and Bronze Highland) has been observed targeting a telecommunications organization in Africa with new plugins...
ChatGPT-Related Malicious URLs on the Rise
The number of newly registered and squatting domains related to ChatGPT grew by 910% monthly between November 2022 and early April 2023. The findings, shared by...
#CYBERUK23: UK Strengthens Cybersecurity Audits for Government Agencies
The UK Government has officially launched GovAssure, a new regime of independent audits of government agencies’ cyber resilience, the Chancellor of the Duchy of Lancaster Oliver...
The EU’s Cyber Solidarity Act: Security Operations Centers to the rescue! – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Márk Szabó. The legislation aims to bolster the Union’s cyber-resilience and enhance its capabilities to prepare for, detect and respond to incidents...
PC running slow? 10 ways you can speed it up – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: André Lameiras. Before you rush to buy new hardware, try these simple tricks to get your machine up to speed again –...
Experts disclosed two critical flaws in Alibaba cloud database services – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Researchers disclosed two critical flaws in Alibaba Cloud’s ApsaraDB RDS for PostgreSQL and AnalyticDB for PostgreSQL. Researchers from cloud security...
Google TAG warns of Russia-linked APT groups targeting Ukraine – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. The researchers from Google TAG are warning of Russia-linked threat actors targeting Ukraine with phishing campaigns. Russia-linked threat actors launched...
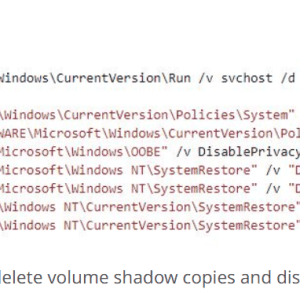
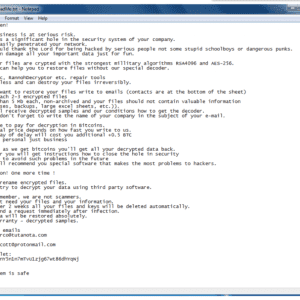
Trigona Ransomware targets Microsoft SQL servers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Threat actors are hacking poorly secured and Interned-exposed Microsoft SQL servers to deploy the Trigona ransomware. Threat actors are hacking...
Russian national sentenced to time served for committing money laundering for the Ryuk ransomware operation – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Russian national Denis Mihaqlovic Dubnikov has been sentenced to time served for committing money laundering for the Ryuk ransomware operation. Russian...
Google fixed the second actively exploited Chrome zero-day of 2023 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Google rolled out emergency security patches to address another actively exploited high-severity zero-day flaw in the Chrome browser. Google rolled...
Why BISOs should oversee policy & report to CROs
By Edwin Doyle, Global Cyber Security Strategist. Cyber security policy is a comprehensive framework consisting of guidelines, protocols, principles and regulations that aim to safeguard an...
Climate change, cyber security and saving the planet
EXECUTIVE SUMMARY: Although the topics of climate change and cyber security seem worlds apart, the reality is that they’re deeply interconnected. The intersection of the two...
RSAC Fireside Chat: How timely intel from the cyber underground improves counter measures
Good intelligence in any theater of war is invaluable. Timely, accurate intel is the basis of a robust defense and can inform potent counterattacks. Related: Ukraine...
What to know: New AI rules in the U.S.
EXECUTIVE SUMMARY: As the fastest-growing consumer application in history, with more than 100 million monthly active users, ChatGPT has gained the attention of lawmakers and policy...
New Zero-Click Exploits Against iOS
HomeBlog New Zero-Click Exploits Against iOS CitizenLab has identified three zero-click exploits against iOS 15 and 16. These were used by NSO Group’s Pegasus spyware in...
RSAC Fireside Chat: StackHawk helps move the application security needle to ‘shift everywhere’
By Byron V. Acohido Embedding security into the highly dynamic way new software gets created and put into service — on the fly, by leveraging ephemeral...
CISO insights on ChatGPT: Game-changer or security threat?
EXECUTIVE SUMMARY: As the AI revolution continues to sweep the world, OpenAI’s ChatGPT tool has emerged as a groundbreaking force in the realm of natural language...
Iranian Hackers Target U.S. Energy and Transit Systems
Mint Sandstorm, an Iranian government-backed actor, has been linked to attacks on critical infrastructure in the United States between late 2021 and mid-2022. The entities that...
Russian Hacktivists Shifting Interest to Business Sector, UK Cyber-agency Warns
The National Cyber Security Centre (NCSC) from the UK issued a warning about state-aligned Russian hacktivists shifting their interest to the business sector. Authorities recommend that...
Trigona Ransomware Deployed Through Vulnerable Microsoft SQL Servers
Attackers are breaking into Microsoft SQL (MS-SQL) servers to install Trigona ransomware payloads and encrypt all files. These servers are not well protected and are exposed...
SIEM vs XDR: A Comparison of Two Advanced Detection and Response Solutions
When trying to tie up your organization’s cybersecurity posture, you look for the perfect detection and response solution to keep you safe. With all the options...
Cryptohack Roundup: Bitrue, Hundred Finance, SafeMoon – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: $10.5M Exploit on 11 Blockchains, MetaMask Third-Party Breach Rashmi...
Emerging Security Concerns About Generative AI in Healthcare – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Generative AI tools such as ChatGPT will undoubtedly change the way clinicians and healthcare cybersecurity professionals work, but the use of...
Why Aren’t 3rd Parties More Transparent About Breaches? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Third-party vendors should be more transparent and faster in communicating when they experience a breach or other security incident that affect...
North Korean Hackers Chained Supply Chain Hacks to Reach 3CX – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Mandiant Concludes 3CX Hack Was Result of Earlier Hack on Trading Software...
Refurbished Routers Contain Sensitive Corporate Data – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Endpoint Security , Hardware / Chip-level Security Eset Finds Customer Info, VPN Credentials & Authentication Keys on Used Routers Prajeet Nair...
Commercial Surveillance Industry Set for Growth, Says NCSC – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Geo Focus: The United Kingdom At Least 80 Countries Have Purchased...
5 Cybersecurity Pillars Where 85% of Companies Are Lagging – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Only 15% of Global Orgs Rank as ‘Mature’ on Cisco’s Cybersecurity Readiness Index Tom Gillis • April 12, 2023 ...
Hundreds of members of congress affected by data breach
DC Health Link, the provider of health insurance for those in the United States (US) Government, has suffered a data breach that affects over 50,000 people. ...