CloudBees flaws in Jenkins server can lead to code executionCloudBees vulnerabilities in the Jenkins open-source automation server can be exploited to achieve code execution on targeted...
Month: March 2023
TSA tells US aviation industry to boost its cybersecurity
TSA tells US aviation industry to boost its cybersecurityThe US Transportation and Security Administration (TSA) has issued new requirements for airport and aircraft operators who, they...
Another Malware with Persistence
Another Malware with PersistenceHere’s a piece of Chinese malware that infects SonicWall security appliances and survives firmware updates. On Thursday, security firm Mandiant published a report...
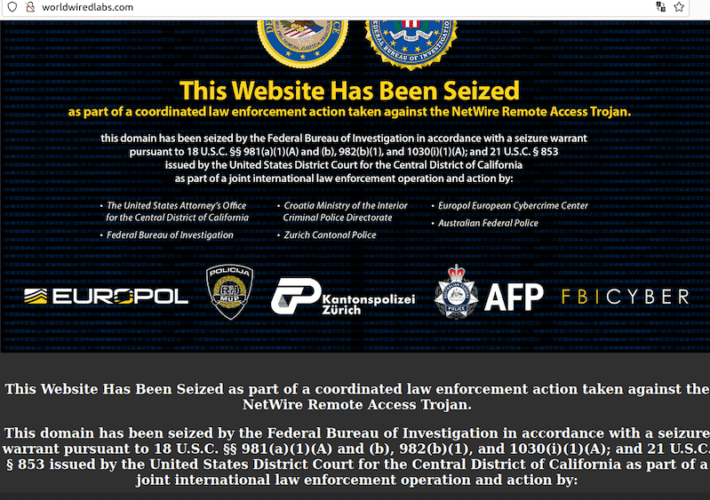
Who’s Behind the NetWire Remote Access Trojan?
Who’s Behind the NetWire Remote Access Trojan?A Croatian national has been arrested for allegedly operating NetWire, a Remote Access Trojan (RAT) marketed on cybercrime forums since...
Amplifying Power to Customer Through Ecosystem Integrations
Amplifying Power to Customer Through Ecosystem IntegrationsTransformation to a SaaS-based cybersecurity vendorRead MoreTrend Micro Research, News, PerspectivesTransformation to a SaaS-based cybersecurity vendor
Remote access policy
Remote access policyPURPOSE This policy outlines guidelines and processes for requesting, obtaining, using and terminating remote access to organization networks, systems and data. It applies to...
GitHub rolling out two-factor authentication to millions of users
GitHub rolling out two-factor authentication to millions of usersOver the next nine months, the largest internet hosting service for software development and collaboration will make all...
Microsoft: Business email compromise attacks can take just hours
Microsoft: Business email compromise attacks can take just hoursMicrosoft's Security Intelligence team recently investigated a business email compromise (BEC) attack and found that attackers move rapidly,...
FBI warns of cryptocurrency theft via “play-to-earn” games
FBI warns of cryptocurrency theft via “play-to-earn” gamesCybercriminals are now using fake rewards in so-called "play-to-earn" mobile and online games to steal millions worth of cryptocurrency, according to...
Akamai mitigates record-breaking 900Gbps DDoS attack in Asia
Akamai mitigates record-breaking 900Gbps DDoS attack in AsiaAkamai reports having mitigated the largest DDoS (distributed denial of service) attack ever launched against a customer based in...
Police seize Netwire RAT malware infrastructure, arrest admin
Police seize Netwire RAT malware infrastructure, arrest adminAn international law enforcement operation involving the FBI and police agencies worldwide led to the arrest of the suspected...
SPAC Woes Continue With Hub Security’s Sluggish Nasdaq Debut
SPAC Woes Continue With Hub Security's Sluggish Nasdaq DebutMeager Product Sales, Limited Presence in Americas Among Red Flags for Hub SecurityThe economic downturn has laid bare...
Webinar | How the SASE Architecture Enables Remote Work
Webinar | How the SASE Architecture Enables Remote WorkPost ContentRead MoreDataBreachToday.com RSS Syndication
Breach Roundup: A Barcelona Hospital, AT&T and Hatch Bank
Breach Roundup: A Barcelona Hospital, AT&T and Hatch BankPlus, Chick-fil-A, Acer & the Online Insurance Marketplace Serving the US CongressHackers disrupted medical care at a major...
Vendor Faces Lawsuit in Wake of an Apparent ‘Royal’ Attack
Vendor Faces Lawsuit in Wake of an Apparent 'Royal' AttackSoftware Firm's Data Exfiltration Health Data Breach Affected Nearly 251,000A healthcare revenue cycle management software vendor is...
CHS to Notify 1 Million in Breach Linked to Software Flaw
CHS to Notify 1 Million in Breach Linked to Software FlawHospital Chain Faults Zero-Day Vulnerability in 3rd-Party File Transfer SoftwareCommunity Health Systems will soon begin notifying...
Cybersecurity Poised for Spending Boost in Biden Budget
Cybersecurity Poised for Spending Boost in Biden BudgetWhite House Proposes Big Boost for CISA and Cybersecurity Aid for UkraineAn overview of the White House's spending blueprint...
Los ataques de Emotet regresan después de una pausa de tres meses
Los ataques de Emotet regresan después de una pausa de tres mesesLa operación de malware Emotet volvió a enviar correos electrónicos no deseados a partir del...
CloudBees flaws in Jenkins server can lead to code execution
CloudBees flaws in Jenkins server can lead to code executionCloudBees vulnerabilities in the Jenkins open-source automation server can be exploited to achieve code execution on targeted...
Airlines and Airports Brace for New TSA Cybersecurity Measures Amidst Persistent Threats
Airlines and Airports Brace for New TSA Cybersecurity Measures Amidst Persistent ThreatsIn the latest move by the Biden administration to strengthen cybersecurity protections for critical infrastructure...
Major Healthcare Data Breach Impacts U.S. House Members
Major Healthcare Data Breach Impacts U.S. House MembersThreat actors breached the DC Health Link network, the healthcare administrator that serves the U.S. House of Representatives. Researchers...
Lazarus Group Hacks South Korean Financial Entity via Zero-Day Vulnerability
Lazarus Group Hacks South Korean Financial Entity via Zero-Day VulnerabilityOver the past year, the Lazarus Group has used flaws in an undisclosed software to breach a...
Putin’s Deepfake Campaign: A New Weapon in the War Against Dissent
Putin’s Deepfake Campaign: A New Weapon in the War Against DissentRussia continues its disinformation campaign around the Ukraine war through advanced social engineering tactics delivered by...
Red Team vs. Blue Team: What Is It?
Red Team vs. Blue Team: What Is It?With cyberattacks seemingly increasing at a high rate, companies have to make sure their details and information are secured...
On the Frontline of the Global Cyber War: Overview of Major russia-backed APT Groups Targeting Ukraine and Sigma Rules to Proactively Defend Against Their TTPs
On the Frontline of the Global Cyber War: Overview of Major russia-backed APT Groups Targeting Ukraine and Sigma Rules to Proactively Defend Against Their TTPs The...
Examining Ransomware Payments From a Data-Science Lens
Examining Ransomware Payments From a Data-Science LensIn this entry, we discuss case studies that demonstrated how data-science techniques were applied in our investigation of ransomware groups'...
Risk management policy
Risk management policySUMMARY Risk management involves the practice of addressing and handling threats to the organization in the form of cybersecurity attacks and compromised or lost...
Become your business’s cybersecurity expert
Become your business’s cybersecurity expertLearn a wide variety of topics for a lifetime with this eclectic bundle. The post Become your business’s cybersecurity expert appeared first...
IceFire ransomware now encrypts both Linux and Windows systems
IceFire ransomware now encrypts both Linux and Windows systemsThreat actors linked to the IceFire ransomware operation are now actively targeting Linux systems worldwide with a new dedicated encryptor....
Protecting collocated servers from DDoS attacks using GRE tunnels
Protecting collocated servers from DDoS attacks using GRE tunnelsYou can get DDoS protection remotely for your collocated server using a generic routing encapsulation (GRE) tunnel. We...