El nuevo malware DotRunpeX ofrece múltiples familias de malware a través de anuncios maliciososUna nueva pieza de malware denominada dotRunpeX se está utilizando para distribuir numerosas...
Month: March 2023
Ferrari confirms data breach after receiving a ransom demand from an unnamed extortion group
Ferrari confirms data breach after receiving a ransom demand from an unnamed extortion groupFerrari disclosed a data breach after receiving a ransom demand from an unnamed...
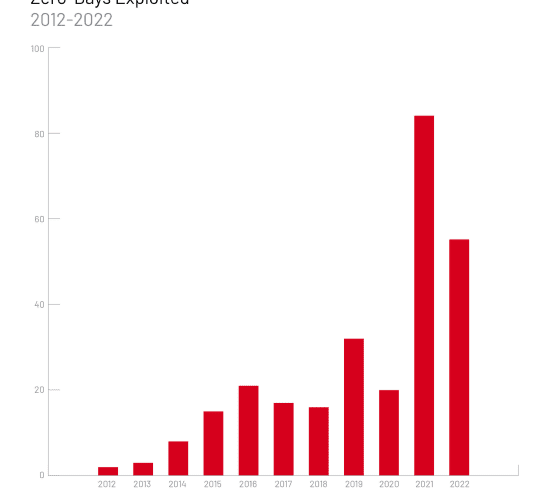
2022 Zero-Day exploitation continues at a worrisome pace
2022 Zero-Day exploitation continues at a worrisome paceExperts warn that 55 zero-day vulnerabilities were exploited in attacks carried out by ransomware and cyberespionage groups in 2022....
New ShellBot bot targets poorly managed Linux SSH Servers
New ShellBot bot targets poorly managed Linux SSH ServersNew ShellBot DDoS bot malware, aka PerlBot, is targeting poorly managed Linux SSH servers, ASEC researchers warn. AhnLab Security...
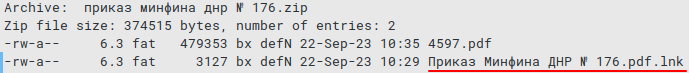
New Bad Magic APT used CommonMagic framework in the area of Russo-Ukrainian conflict
New Bad Magic APT used CommonMagic framework in the area of Russo-Ukrainian conflictThreat actors are targeting organizations located in Donetsk, Lugansk, and Crimea with a previously...
Independent Living Systems data breach impacts more than 4M individuals
Independent Living Systems data breach impacts more than 4M individualsUS health services company Independent Living Systems (ILS) discloses a data breach that impacted more than 4...
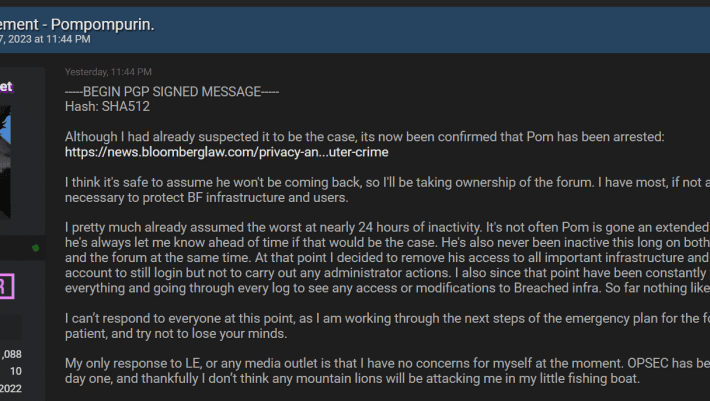
BreachForums current Admin Baphomet shuts down BreachForums
BreachForums current Admin Baphomet shuts down BreachForumsBaphomet, the current administrator of BreachForums, announced that the popular hacking forum has been officially taken down. U.S. law enforcement...
ENISA: Ransomware became a prominent threat against the transport sector in 2022
ENISA: Ransomware became a prominent threat against the transport sector in 2022The European Union Agency for Cybersecurity (ENISA) published its first cyber threat landscape report for...
Experts released PoC exploits for severe flaws in Netgear Orbi routers
Experts released PoC exploits for severe flaws in Netgear Orbi routersCisco Talos researchers published PoC exploits for vulnerabilities in Netgear Orbi 750 series router and extender...
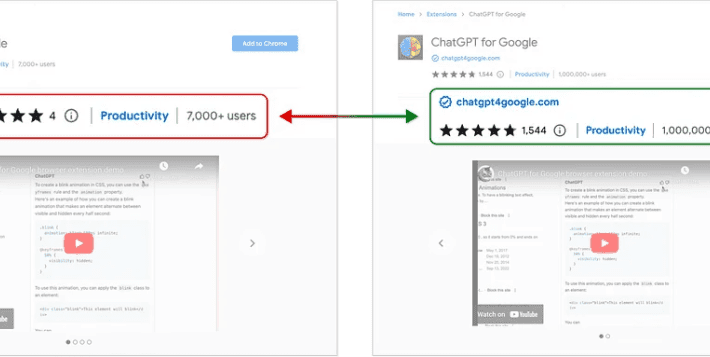
Rogue ChatGPT extension FakeGPT hijacked Facebook accounts
Rogue ChatGPT extension FakeGPT hijacked Facebook accountsA tainted version of the legitimate ChatGPT extension for Chrome, designed to steal Facebook accounts, has thousands of downloads. Guardio’s...
Lionsgate streaming platform with 37m subscribers leaks user data
Lionsgate streaming platform with 37m subscribers leaks user dataEntertainment industry giant Lionsgate leaked users’ IP addresses and information about what content they watch on its movie-streaming...
Banking Trojan Mispadu Found Responsible for 90,000+ Credentials Stolen
Banking Trojan Mispadu Found Responsible for 90,000+ Credentials StolenMultiple spam campaigns targeting Bolivia, Chile, Mexico, Peru, and Portugal have been linked to a banking trojan called...
Ferrari Announces Data Breach. Customers Risk Data Leakage
Ferrari Announces Data Breach. Customers Risk Data LeakageOn March 20th, Ferrari announced they were victims of a cyberattack that could result in customers` data leakage. Threat...
Researchers Reveal Insights into CatB Ransomware’s Advanced Evasion Methods
Researchers Reveal Insights into CatB Ransomware’s Advanced Evasion MethodsTo avoid detection and launch of the payload, threat actors behind CatB ransomware used a technique called DLL...
New PowerMagic and CommonMagic Malware Used by Threat Actors to Steal Data
New PowerMagic and CommonMagic Malware Used by Threat Actors to Steal DataA new backdoor dubbed PowerMagic and “a previously unseen malicious framework” named CommonMagic were utilized...
Another GoAnywhere Attack Affects Japanese Giant Hitachi Energy
Another GoAnywhere Attack Affects Japanese Giant Hitachi EnergyHitachi Energy confirmed that it was the victim of a data breach, part of the GoAnywhere attacks. The Clop...
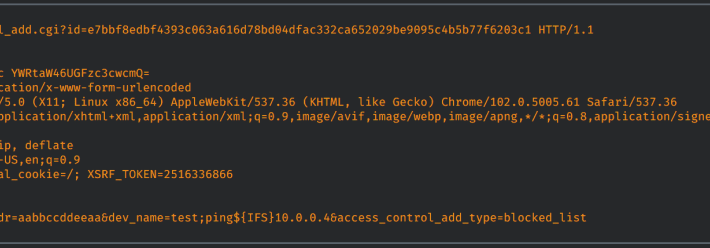
ShellBot DDoS Malware Targets Poorly Managed Linux Servers
ShellBot DDoS Malware Targets Poorly Managed Linux ServersA new campaign is deploying variants of the ShellBot malware, specifically targeting poorly maintained Linux SSH servers. It seems...
The WAN Under Siege
The WAN Under SiegeWAN managers say they’re adopting zero trust security and using multiple infrastructure security vendors in response to the latest threats against the modern...
Stop Backing Up Ransomware
Stop Backing Up RansomwareBy James Gorman When utilizing cloud technology for workloads, companies often assume that their current backup strategy is sufficient for the cloud environment....
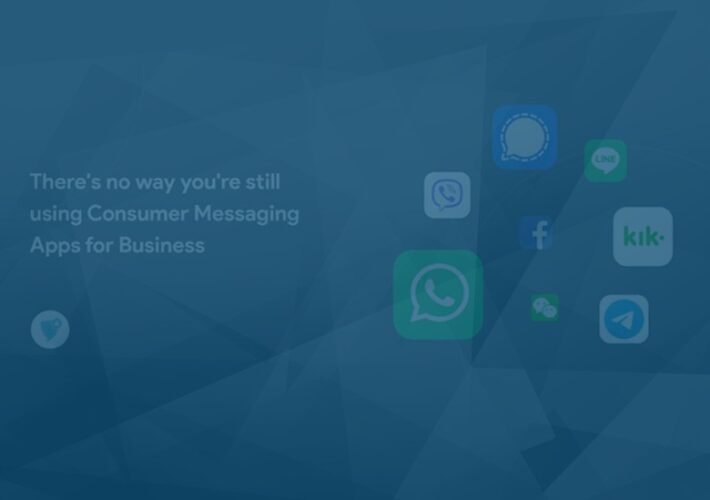
There’s no way you’re still using Consumer Messaging Apps for Business
There’s no way you’re still using Consumer Messaging Apps for BusinessBy Nicole Allen, Senior Marketing Executive, Salt Communications Consumer messaging apps are routinely utilised for business...
Top 5 Questions to Ask When You’re Building a Cloud Security Strategy
Top 5 Questions to Ask When You’re Building a Cloud Security StrategyBy Metin Kortak, chief information security officer, Rhymetec As companies began moving their computing operations...
Vulnerability Prioritization is Not a One-Size Fits All Approach
Vulnerability Prioritization is Not a One-Size Fits All ApproachBy Victor Gamra, CISSP, Founder and CEO of FortifyData System vulnerabilities are ever increasing as adoption of new...
Why Businesses Need to Leverage the NIST Post Quantum Cryptographic Standards to Fortify Their Cybersecurity Future
Why Businesses Need to Leverage the NIST Post Quantum Cryptographic Standards to Fortify Their Cybersecurity FutureBy Dr Ali El Kaafarani, Founder and CEO of PQShield July...
Remaining Proactive at Identifying Risks Keeps You Ahead of Hackers
Remaining Proactive at Identifying Risks Keeps You Ahead of HackersBy Carl Torrence, Content Marketer at Marketing Digest Why is cybersecurity such a big issue in organizations...
Ferrari Data Breach Disclosed: Attackers Gain Access to the Company’s Network While Demanding Ransom to Prevent Data Leakage
Ferrari Data Breach Disclosed: Attackers Gain Access to the Company’s Network While Demanding Ransom to Prevent Data Leakage The massive cyber incident at Ferrari that compromised...
aCropalypse now! Cropped and redacted images suffer privacy fail on Google Pixel smartphones
aCropalypse now! Cropped and redacted images suffer privacy fail on Google Pixel smartphonesHave you ever shared a photograph where you've redacted some sensitive information? Perhaps you've...
The hidden danger to zero trust: Excessive cloud permissions
The hidden danger to zero trust: Excessive cloud permissionsGraham Cluley Security News is sponsored this week by the folks at Sysdig. Thanks to the great team...
Smashing Security podcast #314: Photo cropping bombshell, TikTok debates, and real estate scams
Smashing Security podcast #314: Photo cropping bombshell, TikTok debates, and real estate scamsIt could be a case of aCropalypse now for Google Pixel users, there’s a...
ChatGPT Privacy Flaw
ChatGPT Privacy FlawOpenAI has disabled ChatGPT’s privacy history, almost certainly because they had a security flaw where users were seeing each others’ histories. Read MoreSchneier on...
US Citizen Hacked by Spyware
US Citizen Hacked by SpywareThe New York Times is reporting that a US citizen’s phone was hacked by the Predator spyware. A U.S. and Greek national...