WordPress force patching WooCommerce plugin with 500K installsAutomattic, the company behind the WordPress content management system, is force installing a security update on hundreds of thousands of websites...
Month: March 2023
BlackGuard stealer now targets 57 crypto wallets, extensions
BlackGuard stealer now targets 57 crypto wallets, extensionsA new variant of the BlackGuard stealer has been spotted in the wild, featuring new capabilities like USB propagation,...
Microsoft Teams, Virtualbox, Tesla zero-days exploited at Pwn2Own
Microsoft Teams, Virtualbox, Tesla zero-days exploited at Pwn2OwnDuring the second day of Pwn2Own Vancouver 2023, competitors were awarded $475,000 after successfully exploiting 10 zero-days in multiple...
How AI is helping companies fight document fraud
How AI is helping companies fight document fraudIn an exclusive interview with David Hobbs, a fraud expert at Check Point, Conor Burke, the co-founder and CTO...
What is reverse tabnabbing and how can you stop it?
What is reverse tabnabbing and how can you stop it?EXECUTIVE SUMMARY: Reverse tabnabbing, also known simply as tabnabbing, is a form of phishing that involves deceiving...
Cisco IOS and IOS XE Software IPv6 DHCP (DHCPv6) Relay and Server Denial of Service Vulnerability
Cisco IOS and IOS XE Software IPv6 DHCP (DHCPv6) Relay and Server Denial of Service VulnerabilityA vulnerability in the IPv6 DHCP version 6 (DHCPv6) relay and...
Cisco IOS XE Software for Wireless LAN Controllers HTTP Client Profiling Denial of Service Vulnerability
Cisco IOS XE Software for Wireless LAN Controllers HTTP Client Profiling Denial of Service VulnerabilityA vulnerability in the HTTP-based client profiling feature of Cisco IOS XE...
Live Webinar | The Good, the Bad and the Truth About Password Managers
Live Webinar | The Good, the Bad and the Truth About Password ManagersPost ContentRead MoreDataBreachToday.com RSS Syndication
Breach Roundup: Ferrari, Indian Health Ministry and the NBA
Breach Roundup: Ferrari, Indian Health Ministry and the NBAAlso: Lionsgate, Royal Dirkzwager, New LockBit Claims and Latitude FinancialThis week's roundup of cybersecurity incidents around the world...
Lawmakers Weigh New Regulations in U.S. Cyber Strategy
Lawmakers Weigh New Regulations in U.S. Cyber StrategyDon't 'Overregulate,' GOP Subcommittee Chairwoman Tells White House OfficialMembers of a U.S. House panel got their first look at...
Cryptohack Roundup: BitPay, Euler Finance Gala Games
Cryptohack Roundup: BitPay, Euler Finance Gala GamesAlso: Fireblocks, BitGo Clash; Bitzlato Users can Withdraw Some FundsEvery week, ISMG rounds up cybersecurity incidents in the world of...
SideCopy APT Targets India’s Premier Defense Research Agency
SideCopy APT Targets India's Premier Defense Research AgencySideCopy APT Used Decoy Documents in Spear-Phishing Attack On DRDOSecurity researchers uncovered a Pakistani cyberespionage group employing fresh tactics...
Nuevas variantes de malware ShellBot DDoS dirigidas a servidores Linux mal administrados
Nuevas variantes de malware ShellBot DDoS dirigidas a servidores Linux mal administradosLos servidores Linux SSH mal administrados están siendo el objetivo de una nueva campaña que...
9 attack surface discovery and management tools
9 attack surface discovery and management toolsCyber asset attack surface management (CAASM) or external attack surface management (EASM) solutions are designed to quantify the attack surface...
Developed countries lag emerging markets in cybersecurity readiness
Developed countries lag emerging markets in cybersecurity readinessOrganizations in developed countries are not as prepared for cybersecurity incidents compared to those in developing countries, according to...
BrandPost: Stop the Sprawl: How Vendor Consolidation Can Reduce Security Risks in the Cloud
BrandPost: Stop the Sprawl: How Vendor Consolidation Can Reduce Security Risks in the CloudManaging multiple security vendors is proving to be a significant challenge for organizations,...
As critical Microsoft vulnerabilities drop, attackers may adopt new techniques
As critical Microsoft vulnerabilities drop, attackers may adopt new techniquesWhile the total number of recorded Microsoft vulnerabilities was higher in 2022 than ever before, the number...
Ping Identity debuts decentralized access management system in early access
Ping Identity debuts decentralized access management system in early accessPing Identity, a Colorado-based IAM software vendor, is making a new product, PingOne Neo, available in a...
Sharing sensitive business data with ChatGPT could be risky
Sharing sensitive business data with ChatGPT could be riskyThe furor surrounding ChatGPT remains at a fever pitch as the ins and outs of the AI chatbot’s...
Backslash AppSec solution targets toxic code flows, threat model automation
Backslash AppSec solution targets toxic code flows, threat model automationBackslash Security has announced its launch with a new cloud-native application security (AppSec) solution designed to identify...
Average enterprise storage/backup device has 14 vulnerabilities, three high or critical risks
Average enterprise storage/backup device has 14 vulnerabilities, three high or critical risksThe average enterprise storage and backup device has 14 vulnerabilities, three of which are high...
Landmark UK-Israeli agreement to boost mutual cybersecurity development, tackle shared threats
Landmark UK-Israeli agreement to boost mutual cybersecurity development, tackle shared threatsThe UK and Israeli governments have signed a landmark agreement to define bilateral relations between the...
55 zero-day flaws exploited last year show the importance of security risk management
55 zero-day flaws exploited last year show the importance of security risk managementDeploying security patches as quickly as possible remains one of the best ways to...
Splunk adds new security and observability features
Splunk adds new security and observability featuresNew security and observability features will be added to Splunk Mission Control and its Observability Cloud to identify threats and...
How training and recognition can reduce cybersecurity stress and burnout
How training and recognition can reduce cybersecurity stress and burnoutCybersecurity is a demanding profession that comes with significant stress and burnout — it presents a complex...
New vulnerabilities found in industrial control systems of major vendors
New vulnerabilities found in industrial control systems of major vendorsThe US Cybersecurity and Infrastructure Security Agency (CISA) has issued advisories on 49 vulnerabilities in eight industrial...
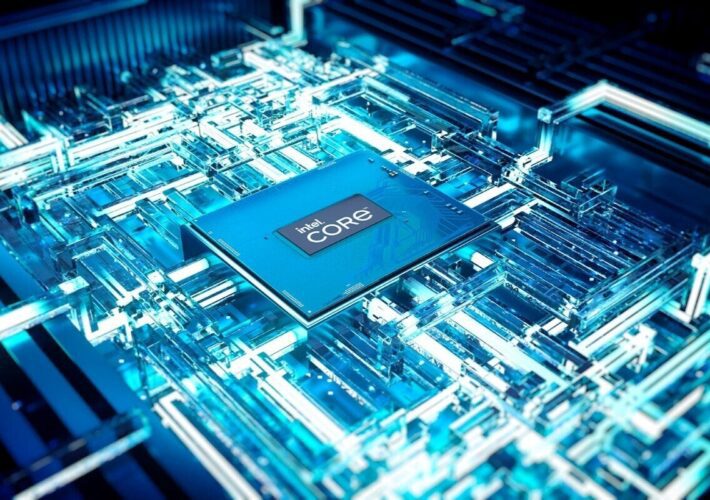
Security at the core of Intel’s new vPro platform
Security at the core of Intel’s new vPro platformIntel has introduced its 13th Generation Core processor line, which the company claims is the first to build...
Understanding Managed Detection and Response – and what to look for in an MDR solution
Understanding Managed Detection and Response – and what to look for in an MDR solutionWhy your organization should consider an MDR solution and five key things...
Ransomware Attacks Double in Europe’s Transport Sector
Ransomware Attacks Double in Europe's Transport SectorENISA claims most threats are opportunisticRead MoreENISA claims most threats are opportunistic
Just 1% of Dot-Org Domains Are Fully DMARC Protected
Just 1% of Dot-Org Domains Are Fully DMARC ProtectedOrganizations are failing with their anti-phishing measuresRead MoreOrganizations are failing with their anti-phishing measures