The metaverse brings a new breed of threats to challenge privacy and security gatekeepersThe metaverse is coming; businesses and government agencies are already building virtual worlds...
Month: January 2023
US Supreme Court leak investigation highlights weak and ineffective risk management strategy
US Supreme Court leak investigation highlights weak and ineffective risk management strategyThe Supreme Court of the United States (SCOTUS) has announced that its investigation to find...
Attackers exploiting critical flaw in many Zoho ManageEngine products
Attackers exploiting critical flaw in many Zoho ManageEngine productsUsers of on-premises deployments of Zoho ManageEngine products should make sure they have patches applied for a critical...
Nvidia targets insider attacks with digital fingerprinting technology
Nvidia targets insider attacks with digital fingerprinting technologyNvidia today announced that a digital lab playground for its latest security offering is now available, letting users try...
Australia fronts International Counter Ransomware Taskforce
Australia fronts International Counter Ransomware TaskforceThe International Counter Ransomware Taskforce (ICRTF), envisioned by the International Counter Ransomware Initiative (CRI), kicked off its operations on Monday with Australia...
Guide: How MSSPs and vCISOs can extend their services into compliance readiness without increasing cost
Guide: How MSSPs and vCISOs can extend their services into compliance readiness without increasing costCompliance services are emerging as one of the hottest areas of cybersecurity. ...
How passkeys are changing authentication
How passkeys are changing authenticationPasswords are a central aspect of security infrastructure and practice, but they are also a principal weakness involved in 81% of all...
Iranian Government Entities Under Attack by New Wave of BackdoorDiplomacy Attacks
Iranian Government Entities Under Attack by New Wave of BackdoorDiplomacy AttacksThe threat actor known as BackdoorDiplomacy has been linked to a new wave of attacks targeting Iranian government...
Earth Bogle Campaign Unleashes NjRAT Trojan on Middle East and North Africa
Earth Bogle Campaign Unleashes NjRAT Trojan on Middle East and North AfricaAn ongoing campaign dubbed Earth Bogle is leveraging geopolitical-themed lures to deliver the NjRAT remote access trojan...
Mailchimp Suffers Another Security Breach Compromising Some Customers’ Information
Mailchimp Suffers Another Security Breach Compromising Some Customers' InformationPopular email marketing and newsletter service Mailchimp has disclosed yet another security breach that enabled threat actors to...
Skyhawk launches platform to provide threat detection and response across multi-cloud environments
Skyhawk launches platform to provide threat detection and response across multi-cloud environmentsCloud threat detection vendor Skyhawk Security has released a platform designed to address alert fatigue...
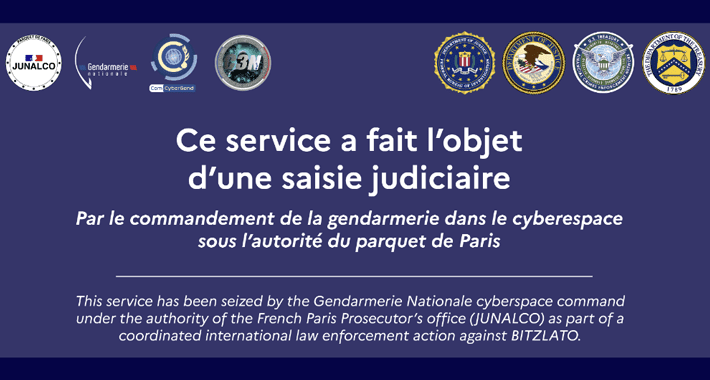
Bitzlato Crypto Exchange Founder Arrested for Aiding Cybercriminals
Bitzlato Crypto Exchange Founder Arrested for Aiding CybercriminalsThe U.S. Department of Justice (DoJ) on Wednesday announced the arrest of Anatoly Legkodymov (aka Gandalf and Tolik), the...
6 Types of Risk Assessment Methodologies + How to Choose
6 Types of Risk Assessment Methodologies + How to ChooseAn organization’s sensitive information is under constant threat. Identifying those security risks is critical to protecting that...
ServiceNow to detect open source security vulnerabilities with Snyk integration
ServiceNow to detect open source security vulnerabilities with Snyk integrationServiceNow Vulnerability Response users will now have access to Snyk Open Source, a software composition analysis (SCA) platform...
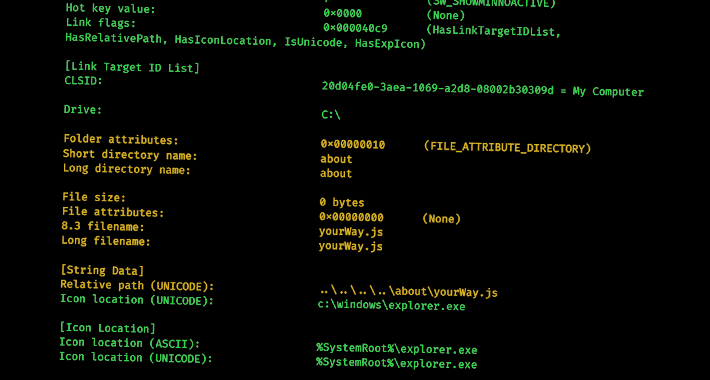
New Research Delves into the World of Malicious LNK Files and Hackers Behind Them
New Research Delves into the World of Malicious LNK Files and Hackers Behind ThemCybercriminals are increasingly leveraging malicious LNK files as an initial access method to...
FBI Confirms Lazarus Group Was Behind $100m Harmony Hack
FBI Confirms Lazarus Group Was Behind $100m Harmony HackThe North Korean cyber actors laundered over $60m worth of Ethereum stolen during the heistLeer másThe North Korean...
DragonSpark Hackers Evade Detection With SparkRAT and Golang
DragonSpark Hackers Evade Detection With SparkRAT and GolangThe new string of attacks mostly targeted East Asian organizationsLeer másThe new string of attacks mostly targeted East Asian...
P-to-P fraud most concerning cyber threat in 2023: CSI
P-to-P fraud most concerning cyber threat in 2023: CSIUS financial institutions see peer-to-peer fraud and other digital fraud as the biggest cybersecurity concern in 2023. It...
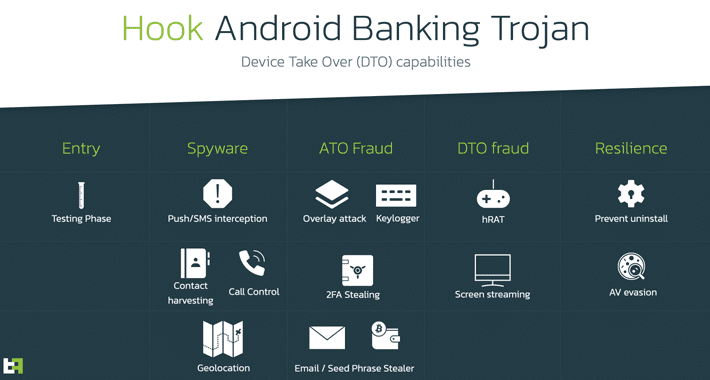
Android Users Beware: New Hook Malware with RAT Capabilities Emerges
Android Users Beware: New Hook Malware with RAT Capabilities EmergesThe threat actor behind the BlackRock and ERMAC Android banking trojans has unleashed yet another malware for rent called Hook that introduces new...
Just Half of Firms Have Sufficient Cybersecurity Budget
Just Half of Firms Have Sufficient Cybersecurity BudgetOne in 10 can only protect critical assets, says NeustarLeer másOne in 10 can only protect critical assets, says...
CYGNVS exits stealth, trumpeting its cyberattack recovery platform
CYGNVS exits stealth, trumpeting its cyberattack recovery platformCyber recovery startup CYGNVS announced its emergence from stealth today, having raised $55 million in series A funding and...
New Cheats May Emerge After Riot Games Hack
New Cheats May Emerge After Riot Games HackRansomware actors stole source code, company revealsLeer másRansomware actors stole source code, company reveals
Veterans bring high-value, real-life experience as potential cybersecurity employees
Veterans bring high-value, real-life experience as potential cybersecurity employeesJohanna Wood was an armored crewman with Lord Strathcona’s Horse, a Canadian Army regiment. At first glance, Wood’s...
New Microsoft Azure Vulnerability Uncovered — EmojiDeploy for RCE Attacks
New Microsoft Azure Vulnerability Uncovered — EmojiDeploy for RCE AttacksA new critical remote code execution (RCE) flaw discovered impacting multiple services related to Microsoft Azure could...
Regulator Stress Test Highlights Cyber Insurance Concerns
Regulator Stress Test Highlights Cyber Insurance ConcernsBank of England warns greater cross-industry consensus is neededLeer másBank of England warns greater cross-industry consensus is needed
Ticketmaster Claims Bot Attack Disrupted Taylor Swift Tour Sales
Ticketmaster Claims Bot Attack Disrupted Taylor Swift Tour SalesJoe Berchtold, president of Live Nation, made the claims at a congressional committee TuesdayLeer másJoe Berchtold, president of...
Yahoo Overtakes DHL As Most Impersonated Brand in Q4 2022
Yahoo Overtakes DHL As Most Impersonated Brand in Q4 2022DHL came in second place, with 16% of all brand phishing attempts, and Microsoft followed with 11%Leer...
APT group trojanizes Telegram app – Week in security with Tony Anscombe
APT group trojanizes Telegram app – Week in security with Tony AnscombeStrongPity's backdoor is fitted with various spying features and can record phone calls, collect texts,...
Chinese Hackers Exploited Recent Fortinet Flaw as 0-Day to Drop Malware
Chinese Hackers Exploited Recent Fortinet Flaw as 0-Day to Drop MalwareA suspected China-nexus threat actor exploited a recently patched vulnerability in Fortinet FortiOS SSL-VPN as a...
North Korean Group TA444 Shows ‘Startup’ Culture, Tries Numerous Infection Methods
North Korean Group TA444 Shows 'Startup' Culture, Tries Numerous Infection MethodsThe threat actor has been targeting cryptocurrency exchanges since at least 2017Leer másThe threat actor has...