I am a Medibank customer. Am I affected by the cyber-attack? What can I do to protect myself?Experts suggest using multifactor authentication and telling your bank...
Year: 2022
K45012029: OpenJDK vulnerability CVE-2020-14796, CVE-2020-14798, CVE-2020-14803
K45012029: OpenJDK vulnerability CVE-2020-14796, CVE-2020-14798, CVE-2020-14803OpenJDK vulnerability CVE-2020-14796, CVE-2020-14798, CVE-2020-14803 Security Advisory Security Advisory Description CVE-2020-14796 Vulnerability in the Java SE, Java SE Embedded product of...
K45012029: OpenJDK vulnerability CVE-2020-14796, CVE-2020-14798, CVE-2020-14803
K45012029: OpenJDK vulnerability CVE-2020-14796, CVE-2020-14798, CVE-2020-14803OpenJDK vulnerability CVE-2020-14796, CVE-2020-14798, CVE-2020-14803 Security Advisory Security Advisory Description CVE-2020-14796 Vulnerability in the Java SE, Java SE Embedded product of...
See Yourself in Cyber: 5 Questions with Amelina Ishak
See Yourself in Cyber: 5 Questions with Amelina IshakIn celebration of this year’s Cybersecurity Awareness Month theme – See Yourself in Cyber – we are spotlighting...
See Yourself in Cyber: 5 Questions with Amelina Ishak
See Yourself in Cyber: 5 Questions with Amelina IshakIn celebration of this year’s Cybersecurity Awareness Month theme – See Yourself in Cyber – we are spotlighting...
Cybereason Lays Off Another 200 Workers Amid Report of Sale
Cybereason Lays Off Another 200 Workers Amid Report of SaleCybereason's Latest Layoffs Come Less Than 5 Months After Company Cut Staff by 10%Cybereason has carried out...
K41454238: Apache mod_auth_openidc vulnerabilities CVE-2021-32785 CVE-2021-32786 CVE-2021-32792
K41454238: Apache mod_auth_openidc vulnerabilities CVE-2021-32785 CVE-2021-32786 CVE-2021-32792Apache mod_auth_openidc vulnerabilities CVE-2021-32785 CVE-2021-32786 CVE-2021-32792 Security Advisory Security Advisory Description CVE-2021-32785 mod_auth_openidc is an authentication/ ... More info: https://support.f5.com/csp/article/K41454238?utm_source=f5support&utm_medium=RSSLeer...
K41454238: Apache mod_auth_openidc vulnerabilities CVE-2021-32785 CVE-2021-32786 CVE-2021-32792
K41454238: Apache mod_auth_openidc vulnerabilities CVE-2021-32785 CVE-2021-32786 CVE-2021-32792Apache mod_auth_openidc vulnerabilities CVE-2021-32785 CVE-2021-32786 CVE-2021-32792 Security Advisory Security Advisory Description CVE-2021-32785 mod_auth_openidc is an authentication/ ... More info: https://support.f5.com/csp/article/K41454238?utm_source=f5support&utm_medium=RSSLeer...
K11601010: Intel Processor vulnerability CVE-2021-33149
K11601010: Intel Processor vulnerability CVE-2021-33149Intel Processor vulnerability CVE-2021-33149 Security Advisory Security Advisory Description Observable behavioral discrepancy in some Intel(R) Processors may allow an authorized user to...
K11601010: Intel Processor vulnerability CVE-2021-33149
K11601010: Intel Processor vulnerability CVE-2021-33149Intel Processor vulnerability CVE-2021-33149 Security Advisory Security Advisory Description Observable behavioral discrepancy in some Intel(R) Processors may allow an authorized user to...
UK Data Watchdog Issues Warning on Emotional Detection Tech
UK Data Watchdog Issues Warning on Emotional Detection TechUK ICO Promises Biometrics Guidance Document in Spring 2023Artificial intelligence-driven technology purporting to recognize human emotional states "may...
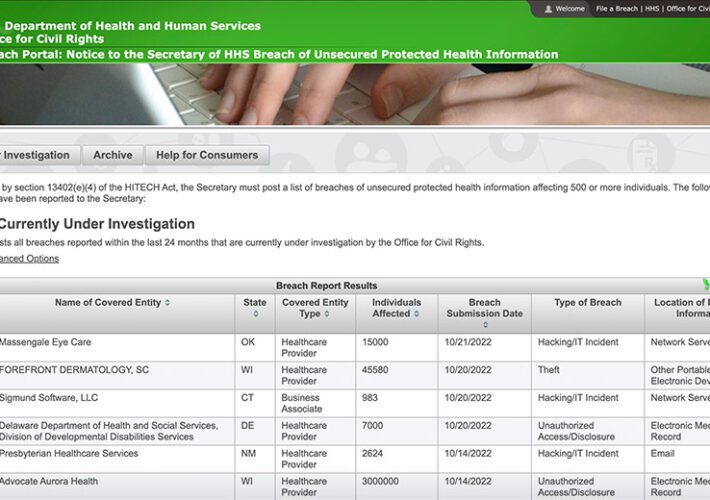
Federal Tally Reaches 5,000 Health Data Breaches Since 2009
Federal Tally Reaches 5,000 Health Data Breaches Since 2009More People Affected by Breaches Than Total US PopulationThe federal tally of health data breaches reached a new...
Zero-Day Hoarding Aids Advanced Spyware, PEGA Committee Told
Zero-Day Hoarding Aids Advanced Spyware, PEGA Committee ToldGoogle's Shane Huntley Urges EU to 'Lead a Diplomatic Effort' to Curb SpywareThe problem of zero-day exploits used by...
Network Detection and Response (NDR) vs. Endpoint Detection and Response (EDR): A Comparison
Network Detection and Response (NDR) vs. Endpoint Detection and Response (EDR): A ComparisonAs the rate of cybersecurity incidents increases and cybercriminals are more creative in deploying...
Linux Patch Management: Challenges, Benefits and Best Practices
Linux Patch Management: Challenges, Benefits and Best PracticesIn comparison with Windows, Linux it’s different in areas such as features, flexibility, operationality, and ease of use. Naturally,...
What Are the Main Attack Vectors in Cybersecurity?
What Are the Main Attack Vectors in Cybersecurity?Today’s dangerous cyber landscape demands all businesses to position themselves ahead of cybercriminals in order to maintain their safety....
Massive Typosquatting Campaign Uses over 200 Fake Domains
Massive Typosquatting Campaign Uses over 200 Fake DomainsAn ongoing campaign tricks users to download several Windows and Android malware from typosquatting domains. The massive malicious campaign is...
There’s good and bad news about the Microsoft Exchange server zero-day exploit
There’s good and bad news about the Microsoft Exchange server zero-day exploitYay, Microsoft has told us how to mitigate against the recently-discovered zero-day attacks. Boo, the...
CISA: Daixin Team Is Targeting U.S. Healthcare in Ransomware Attacks
CISA: Daixin Team Is Targeting U.S. Healthcare in Ransomware AttacksA cybercriminal group called Daixin Team is actively launching ransomware attacks against the U.S. healthcare sector. CISA,...
Student data leaked after LA school district says it won’t pay ransom
Student data leaked after LA school district says it won’t pay ransomHackers have leaked data stolen from the United States's second-largest school district, after the Los...
METRO Confirms Cyberattack Caused IT Outage
METRO Confirms Cyberattack Caused IT OutageInternational retailer METRO has confirmed a recent cyberattack that causing infrastructure outages and store payment issues. With more than 95,000 employees in...
CISA orders federal agencies to catalog their networks, and scan for bugs
CISA orders federal agencies to catalog their networks, and scan for bugsYou always want to know what is attached to your network. And whether it could...
Kolide can help you nail audits and compliance goals with endpoint security for your entire fleet
Kolide can help you nail audits and compliance goals with endpoint security for your entire fleetGraham Cluley Security News is sponsored this week by the folks...
5 tips to help children navigate the internet safely
5 tips to help children navigate the internet safelyThe online world provides children with previously unimagined opportunities to learn and socialize, but it also opens them...
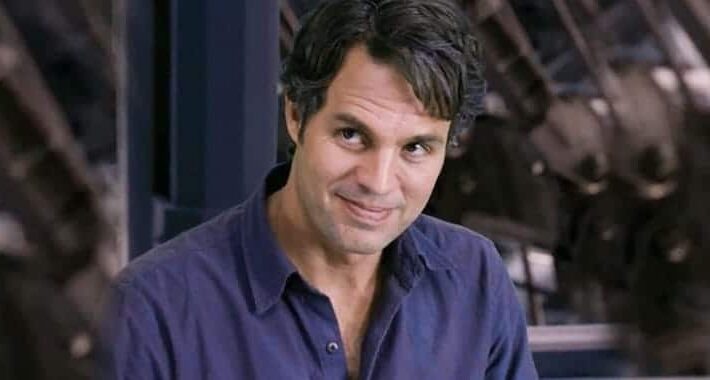
How a deepfake Mark Ruffalo scammed half a million dollars from a lonely heart
How a deepfake Mark Ruffalo scammed half a million dollars from a lonely heartA 74-year-old Manga artist received an unsolicited Facebook message from somebody claiming to...
What to consider before disposing of personal data – Week in security with Tony Anscombe
What to consider before disposing of personal data – Week in security with Tony AnscombeA major financial services company has learned the hard way about the...
What happens with a hacked Instagram account – and how to recover it
What happens with a hacked Instagram account – and how to recover itHad your Instagram account stolen? Don’t panic – here’s how to get your account...
Smashing Security podcast #292: Trussterflucks and eBay stalking
Smashing Security podcast #292: Trussterflucks and eBay stalkingHas new UK prime minister Liz Truss been careless with her mobile phone, and hear the most extraordinary story...
New Windows Zero-Day Vulnerability Lets JavaScript Files Bypass Security Warnings
New Windows Zero-Day Vulnerability Lets JavaScript Files Bypass Security WarningsA new Windows zero-day bug has been used by threat actors in ransomware attacks. The vulnerability allows...
Protecting teens from sextortion: What parents should know
Protecting teens from sextortion: What parents should knowOnline predators increasingly trick or coerce youth into sharing explicit videos and photos of themselves before threatening to post...