14 PCI Compliance security best practices for your businessLooking for more information on PCI Compliance security? Read 14 security best practices for PCI (Payment Card Industry)...
Year: 2022
The Cybersecurity Industry is Broken
The Cybersecurity Industry is BrokenThe security industry must transform. Tom Corn, Senior Vice President, Security Products at VMware, knows where to begin. Cloud can be the...
Operation Elaborate – UK police text 70,000 people thought to have fallen victim to iSpoof bank fraudsters
Operation Elaborate – UK police text 70,000 people thought to have fallen victim to iSpoof bank fraudstersUK police are texting 70,000 people who they believe have...
Security At The Forefront: A Spotlight On Zero Trust
Security At The Forefront: A Spotlight On Zero TrustVMware commissioned Forrester Consulting to evaluate how organizations are working to ensure a strong security posture via Zero...
How CIOs Should Think About Blockchain
How CIOs Should Think About BlockchainFrom a security standpoint, blockchain represents an opportunity to reinforce the foundation of your business, but it’s important to look at...
CIO Essential Guidance: CISO Security Threat landscape
CIO Essential Guidance: CISO Security Threat landscapeDespite massive spend to protect enterprise digital assets, security breaches are still on the rise. The disconnect between the level...
What is Antivirus and What Does It Really Protect?
What is Antivirus and What Does It Really Protect? Authored by Dennis Pang What is antivirus? That’s a good question. What does it really protect? That’s...
McAfee Personal Data Cleanup: Your Partner in Living a More Private Online Life
McAfee Personal Data Cleanup: Your Partner in Living a More Private Online Life Do yourself a favor: Open a new browser tab and head to your...
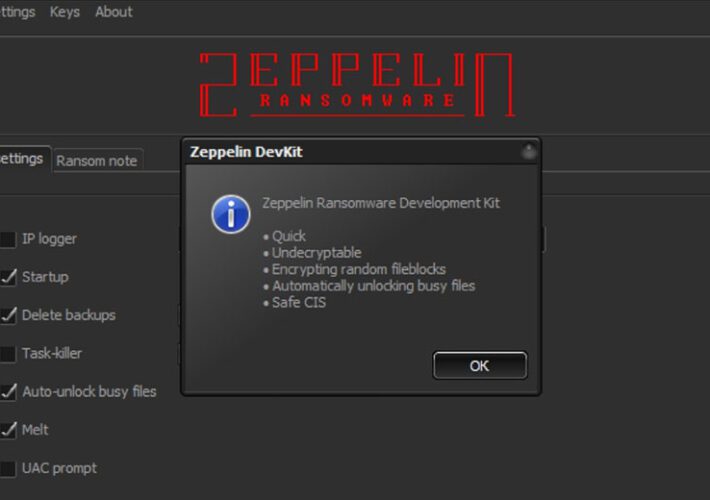
Zeppelin Ransomware Proceeds Punctured by Crypto Workaround
Zeppelin Ransomware Proceeds Punctured by Crypto WorkaroundCryptography Errors Exploited by Researchers for Recovery Without Paying a RansomAs the U.S. celebrates Thanksgiving, let's give thanks for this...
Solving The Cybersecurity Talent Crisis Demands Public-Private Sector Collaboration
Solving The Cybersecurity Talent Crisis Demands Public-Private Sector CollaborationContenido de la entradaLeer másProofpoint News Feed
Top 5 confidential computing uses in healthcare
Top 5 confidential computing uses in healthcareBig data meets private data in a perfect storm for healthcare. Confidential computing providers say they’ll make the cloud safer...
SocGholish finds success through novel email techniques
SocGholish finds success through novel email techniquesContenido de la entradaLeer másProofpoint News Feed
Cybercrime Carnage: Cryptocurrency-Targeting Attacks Abound
Cybercrime Carnage: Cryptocurrency-Targeting Attacks AboundFrom Cryptojacking to Exchange Hacks to Scam Token Contracts, Innovation AboundsWhile the cybercrime story for 2022 has yet to be fully written,...
GUEST ESSAY: What ‘self-sovereign-identities’ are all about — and how SSIs can foster public good
GUEST ESSAY: What ‘self-sovereign-identities’ are all about — and how SSIs can foster public goodGovernment assistance can be essential to individual wellbeing and economic stability. This...
MSA-22-0031: Stored XSS possible in some "social" user profile fields
MSA-22-0031: Stored XSS possible in some "social" user profile fieldsby Michael Hawkins. The "social" user profile field type performed insufficient escaping on some fields, resulting in...
MSA-22-0029: Course restore – CSRF token passed in course redirect URL
MSA-22-0029: Course restore - CSRF token passed in course redirect URLby Michael Hawkins. A users CSRF token was unnecessarily included in the URL when being redirected...
MSA-22-0030: Reflected XSS risk in policy tool
MSA-22-0030: Reflected XSS risk in policy toolby Michael Hawkins. The return URL in the policy tool required extra sanitizing to prevent a reflected XSS risk.Severity/Risk:SeriousVersions affected:4.0...
MSA-22-0028: Apply upstream security fix to VideoJS library to remove XSS risk
MSA-22-0028: Apply upstream security fix to VideoJS library to remove XSS riskby Michael Hawkins. An upstream security patch was applied to the third party VideoJS library...
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part4 (Dacls, aka MATA)
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part4 (Dacls, aka MATA)Dacls, aka MATA, is a cross-platform RAT used by the DPRK-linked Lazarus Group and the...
Setting the Record Straight on XDR at VMware Explore Europe
Setting the Record Straight on XDR at VMware Explore EuropeThere seems to be a bit of confusion as to what constitutes XDR (extended detection and response)....
K82567234: NodeJS vulnerability CVE-2022-32215
K82567234: NodeJS vulnerability CVE-2022-32215NodeJS vulnerability CVE-2022-32215 Security Advisory Security Advisory Description The llhttp parser <v14.20.1, <v16.17.1 and <v18.9.1 in the http module in Node.js does not...
Addressing the Shortage of Medical Device Cyber Talent
Addressing the Shortage of Medical Device Cyber TalentThe shortage of cybersecurity professionals in the United States includes a scarcity of expertise in medical device security, says...
MEPs’ spyware inquiry targeted by disinformation campaign, say experts
MEPs’ spyware inquiry targeted by disinformation campaign, say expertsEuropean parliament is investigating Pegasus, a powerful surveillance tool used by governments around the world Victims of spyware...
Gangs of cybercriminals are expanding across Africa, investigators say
Gangs of cybercriminals are expanding across Africa, investigators sayOnline scams such as banking and credit card fraud are the most prevalent cyberthreat, says Interpol Police and...
Ransomware Group Zeppelin’s Costly Encryption Mistake
Ransomware Group Zeppelin's Costly Encryption MistakeThe latest edition of the ISMG Security Report discusses how the profits of ransomware group Zeppelin have been smashed by security...
Ontario Teachers’ Data Stolen in Ransomware Attack
Ontario Teachers’ Data Stolen in Ransomware AttackVictims Notified of Ransomware Attack Six Months After the IncidentA cyberattack on a Canadian teachers’ union gave thieves access to...
Multiple Arrests in Coordinated African Cyber Operation
Multiple Arrests in Coordinated African Cyber OperationLaw Enforcement Agencies Also Took Down 200,000 Cyber Infrastructure CrooksA 27-nation joint investigation in Africa led to the arrest of...
Cyber Resilience Minimizes Risks for Digital Services
Cyber Resilience Minimizes Risks for Digital ServicesResiliency Leader Kris Lovejoy on the Convergence of Security and Disaster RecoveryCyber resilience extends beyond cyberattacks and encompasses the convergence...
SharkBot Trojan Spread Via Android File Manager Apps
SharkBot Trojan Spread Via Android File Manager AppsNow-Removed Apps Have 10K Downloads, Target Victims in the UK, ItalyThe operators behind the banking Trojan SharkBot are targeting...
Millones de dispositivos Android aún no tienen parches para fallas en la GPU de Mali
Millones de dispositivos Android aún no tienen parches para fallas en la GPU de MaliUn conjunto de cinco fallas de seguridad de gravedad media en el...