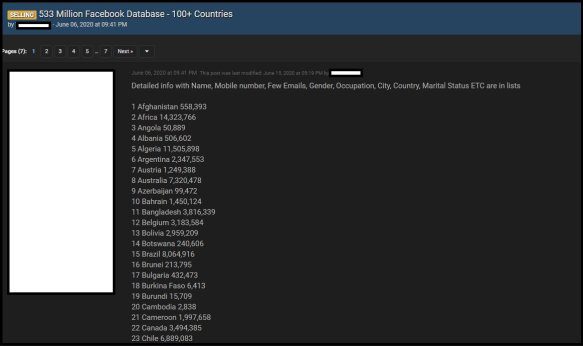
Ireland’s DPC Fines Meta €265m Following Large-Scale Data LeakThe fine followed an inquiry into data processing by Meta in response to a major data breachLeer másThe...
Year: 2022
Police Shutter 13,000 Sites in Piracy Crackdown
Police Shutter 13,000 Sites in Piracy CrackdownFourteen detained as part of Europol operationLeer másFourteen detained as part of Europol operation
Meta fined €265M for not protecting Facebook users’ data from scrapers
Meta fined €265M for not protecting Facebook users' data from scrapersMeta has been fined €265 million ($275.5 million) by the Irish data protection commission (DPC) for a massive...
US Census Bureau Head Fends Off Critics of ‘Differential Privacy’ Tool
US Census Bureau Head Fends Off Critics of 'Differential Privacy' ToolSantos defended differential privacy against prominent researchersLeer másSantos defended differential privacy against prominent researchers
Trending TikTok Challenge Used to Deploy Malware
Trending TikTok Challenge Used to Deploy MalwareTikTok is undoubtedly one of the most popular social media outlets, and as a consequence, hackers are not far behind...
Cyber Monday deal: Get 50% off Malwarebytes Premium, Privacy VPN
Cyber Monday deal: Get 50% off Malwarebytes Premium, Privacy VPNMalwarebytes' Cyber Monday deal is now live, offering a 50% discount on the Malwarebytes Premium antivirus + Malwarebytes Privacy VPN bundle...
PII May Have Been Stolen in Virginia County Ransomware Attack
PII May Have Been Stolen in Virginia County Ransomware AttackA W-2 form was reportedly published on a dark web forum with stolen, sensitive dataLeer másA W-2...
The U.S. Bans the Sale of Huawei, ZTE, and Other Chinese Manufacturers’ Equipment
The U.S. Bans the Sale of Huawei, ZTE, and Other Chinese Manufacturers’ EquipmentThe Federal Communications Commission (FCC), on the behalf of the United States government, adopted...
Experts found a vulnerability in AWS AppSync
Experts found a vulnerability in AWS AppSyncAmazon Web Services (AWS) fixed a cross-tenant vulnerability that could have allowed attackers to gain unauthorized access to resources. Amazon...
TikTok ‘Invisible Body’ challenge exploited to push malware
TikTok ‘Invisible Body’ challenge exploited to push malwareHackers are capitalizing on a trending TikTok challenge named 'Invisible Challenge' to install malware on thousands of devices and...
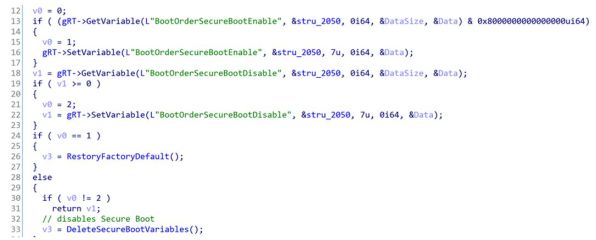
A flaw in some Acer laptops can be used to bypass security features
A flaw in some Acer laptops can be used to bypass security featuresESET announced the discovery of a vulnerability impacting Acer laptops that can allow an...
Irish data protection commission fines Meta over 2021 data-scraping leak
Irish data protection commission fines Meta over 2021 data-scraping leakIrish data protection commission (DPC) fined Meta for not protecting Facebook’s users’ data from scraping. Meta has...
Punisher Ransomware Uses a COVID Lure to Spread
Punisher Ransomware Uses a COVID Lure to SpreadA new variant of Punisher ransomware was discovered recently. The malware spreads through a fake COVID tracking application and...
Oracle Fusion Middleware Vulnerability Actively Exploited in the Wild: CISA
Oracle Fusion Middleware Vulnerability Actively Exploited in the Wild: CISAThe bug allows unauthenticated attackers with network access to compromise Oracle Access ManagerLeer másThe bug allows unauthenticated...
What You Need to Know About the Malicious Android App That’s Powering A Spam Service
What You Need to Know About the Malicious Android App That’s Powering A Spam ServiceA fake Android app downloaded over 100,000 times on the Google Play...
Malicious Android app found powering account creation service
Malicious Android app found powering account creation serviceA fake Android SMS application, with 100,000 downloads on the Google Play store, has been discovered to secretly act...
Acer fixes UEFI bugs that can be used to disable Secure Boot
Acer fixes UEFI bugs that can be used to disable Secure BootAcer has fixed a high-severity vulnerability affecting multiple laptop models that could enable local attackers...
Microsoft Defender boosts default protection for all enterprise users
Microsoft Defender boosts default protection for all enterprise usersMicrosoft announced that built-in protection is generally available for all devices onboarded to Defender for Endpoint, the company's...
SOC Prime Launches Sigma Rules Bot for Threat Bounty
SOC Prime Launches Sigma Rules Bot for Threat Bounty Create, Verify, and Get Sigma Rules Published via Slack SOC Prime is thrilled to announce that Sigma...
Detecting QakBot Malware Campaign Leading to Black Basta Ransomware Infections
Detecting QakBot Malware Campaign Leading to Black Basta Ransomware Infections Ransomware is a number one threat posing a significant menace to security defenders worldwide, with the...
Ransomware detection with Wazuh SIEM and XDR platform
Ransomware detection with Wazuh SIEM and XDR platformWazuh is a free, open source SIEM/XDR solution with more than 10 million annual downloads. Learn more about how...
Computer Repair Technicians Are Stealing Your Data
Computer Repair Technicians Are Stealing Your DataLaptop technicians routinely violate the privacy of the people whose computers they repair: Researchers at University of Guelph in Ontario,...
U.S. Govt. Apps Bundled Russian Code With Ties to Mobile Malware Developer
U.S. Govt. Apps Bundled Russian Code With Ties to Mobile Malware DeveloperA recent scoop by Reuters revealed that mobile apps for the U.S. Army and the Centers...
Charles V of Spain Secret Code Cracked
Charles V of Spain Secret Code CrackedDiplomatic code cracked after 500 years: In painstaking work backed by computers, Pierrot found “distinct families” of about 120 symbols...
What Are Tailgating Attacks and How to Protect Yourself From Them
What Are Tailgating Attacks and How to Protect Yourself From ThemWhether you’re spending time on the web or working in the office, you want peace of...
AWS re:Invent 2022: Partners on parade
AWS re:Invent 2022: Partners on paradeThere's news from Amazon Web Services' Las Vegas show as a flurry of partnerships and edge computing initiatives have been revealed....
A Q&A with Mimi Keshani, COO and Co-Founder of Hadean
A Q&A with Mimi Keshani, COO and Co-Founder of HadeanMimi Keshani is Hadean’s COO, driving its pioneering work in defense and the metaverse. With a strong background in technological sciences,...
Password management policy
Password management policyPassword-driven security may not be the perfect solution, but the alternatives haven’t gained much traction. This policy defines best practices that will make password...
Spanish police dismantle operation that made €12M via investment scams
Spanish police dismantle operation that made €12M via investment scamsSpanish National Police have dismantled a cybercrime organization that used fake investment sites to defraud over €12.3...
Cyber Crime: INTERPOL Uses Trend Threat Intelligence
Cyber Crime: INTERPOL Uses Trend Threat IntelligenceINTERPOL recently conducted operation African Surge to take down malicious infrastructure across the African continent and requested the help of...