Twitter Exposes Personal Information for 5.4 Million AccountsTwitter accidentally exposed the personal information—including phone numbers and email addresses—for 5.4 million accounts. And someone was trying to...
Year: 2022
A Taxonomy of Access Control
A Taxonomy of Access ControlMy personal definition of a brilliant idea is one that is immediately obvious once it’s explained, but no one has thought of...
Friday Squid Blogging: SQUID Acronym for Making Conscious Choices
Friday Squid Blogging: SQUID Acronym for Making Conscious ChoicesI think the U is forced: SQUID consists of five steps: Stop, Question, Understand, Imagine, and Decide. As...
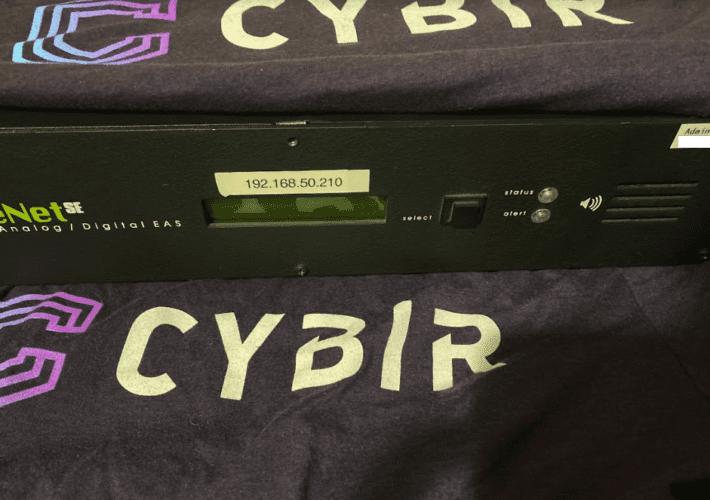
Sounding the Alarm on Emergency Alert System Flaws
Sounding the Alarm on Emergency Alert System FlawsThe Department of Homeland Security (DHS) is urging states and localities to beef up security around proprietary devices that...
Back to School: Tech Savvy vs. Cyber Savvy
Back to School: Tech Savvy vs. Cyber Savvy The first day of school is right around the corner. The whole family is gearing up for a...
Identity and Access Management at NIST: A Rich History and Dynamic Future
Identity and Access Management at NIST: A Rich History and Dynamic FutureDigital identity for access control is a fundamental and critical cybersecurity capability that ensures the...
Chinese hackers backdoor chat app with new Linux, macOS malware
Chinese hackers backdoor chat app with new Linux, macOS malwareVersions of a cross-platform instant messenger application focused on the Chinese market known as 'MiMi' have been...
Microsoft: We Don’t Want to Zero-Day Our Customers
Microsoft: We Don't Want to Zero-Day Our CustomersThe head of Microsoft's Security Response Center defends keeping its initial vulnerability disclosures sparse — it is, she says,...
Best penetration testing tools: 2022 buyer’s guide
Best penetration testing tools: 2022 buyer’s guideSecurity professionals need penetration testing tools to understand the security posture of every software environment. Check out our list of...
How to Clear Security Obstacles and Achieve Cloud Nirvana
How to Clear Security Obstacles and Achieve Cloud NirvanaBack-end complexity of cloud computing means there's plenty of potential for security problems. Here's how to get a...
Novel Ransomware Comes to the Sophisticated SOVA Android Banking Trojan
Novel Ransomware Comes to the Sophisticated SOVA Android Banking TrojanUnusually, SOVA, which targets US users, now allows lateral movement for deeper data access. Version 5 adds...
Software Supply Chain Chalks Up a Security Win With New Crypto Effort
Software Supply Chain Chalks Up a Security Win With New Crypto EffortGitHub, the owner of the Node Package Manager (npm), proposes cryptographically linking source code and...
Palo Alto bug used for DDoS attacks and there’s no fix yet
Palo Alto bug used for DDoS attacks and there's no fix yetThere goes the weekend... A high-severity Palo Alto Networks denial-of-service (DoS) vulnerability has been exploited...
Latin America: A region of challenges and opportunities
Latin America: A region of challenges and opportunitiesFrancisco Robayo is a cyber security expert with 15 years of experience in the sector and more than 20...
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...
Cisco hacked by Yanluowang ransomware gang, 2.8GB allegedly stolen
Cisco hacked by Yanluowang ransomware gang, 2.8GB allegedly stolenCisco confirmed today that the Yanluowang ransomware group breached its corporate network in late May and that the...
Ransomware gangs move to ‘callback’ social engineering attacks
Ransomware gangs move to 'callback' social engineering attacksAt least three groups split from the Conti ransomware operation have adopted BazarCall phishing tactics as the primary method...
Automotive supplier breached by 3 ransomware gangs in 2 weeks
Automotive supplier breached by 3 ransomware gangs in 2 weeksAn automotive supplier had its systems breached and files encrypted by three different ransomware gangs over a two-week...
7-Eleven Denmark confirms ransomware attack behind store closures
7-Eleven Denmark confirms ransomware attack behind store closures7-Eleven Denmark has confirmed that a ransomware attack was behind the closure of 175 stores in the country on...
New dark web markets claim association with criminal cartels
New dark web markets claim association with criminal cartelsSeveral new marketplaces have appeared on the dark web, claiming to be the dedicated online portals for notorious...
GitHub’s new privacy policy sparks backlash over tracking cookies
GitHub's new privacy policy sparks backlash over tracking cookiesDevelopers are furious at GitHub's upcoming privacy policy changes that would allow GitHub to place tracking cookies on some of its...
Access to hacked corporate networks still strong but sales fall
Access to hacked corporate networks still strong but sales fallStatistics collected by cyber-intelligence firm KELA during this year's second quarter show that marketplaces selling initial access...
UK NHS service recovery may take a month after MSP ransomware attack
UK NHS service recovery may take a month after MSP ransomware attackManaged service provider (MSP) Advanced confirmed that a ransomware attack on its systems caused the disruption...
Defend your network with Microsoft outside-in security services
Defend your network with Microsoft outside-in security servicesSeeing your assets the way an attacker would look at them can help you spot where you’re exposed before...
FBI: Zeppelin ransomware may encrypt devices multiple times in attacks
FBI: Zeppelin ransomware may encrypt devices multiple times in attacksThe Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) warned US organizations...
85% of Android users are concerned about privacy
85% of Android users are concerned about privacyGoogle’s security guidelines also drew the majority of this year’s requests in apps, according to Kaspersky’s Privacy Checker website....
Microsoft 365 version 2206 update pulled due to apps crashing
Microsoft 365 version 2206 update pulled due to apps crashingMicrosoft has pulled the Microsoft 365 version 2206 update after users report their Office applications are crashing...
Cisco reveals cyberattack on its corporate network
Cisco reveals cyberattack on its corporate networkThough cybercriminals have published a list of breached files, Cisco said that no sensitive customer or employee data was compromised...
CopperStealer Distributes Malicious Chromium-based Browser Extension to Steal Cryptocurrencies
CopperStealer Distributes Malicious Chromium-based Browser Extension to Steal CryptocurrenciesWe tracked the latest deployment of the group behind CopperStealer, this time stealing cryptocurrencies and users’ wallet account...
Zimbra auth bypass bug exploited to breach over 1,000 servers
Zimbra auth bypass bug exploited to breach over 1,000 serversAn authentication bypass Zimbra security vulnerability is being exploited to compromise Zimbra Collaboration Suite (ZCS) email servers worldwide....