North Korean Lazarus hackers take aim at U.S. energy providersThe North Korean APT group 'Lazarus' (APT38) is exploiting VMWare Horizon servers to access the corporate networks...
Year: 2022
Classified NATO documents stolen from Portugal, now sold on darkweb
Classified NATO documents stolen from Portugal, now sold on darkwebThe Armed Forces General Staff agency of Portugal (EMGFA) has suffered a cyberattack that allegedly allowed the...
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel Sectors
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel SectorsContenido de la entradaLeer másProofpoint News Feed
Over 80% of the top websites leak user searches to advertisers
Over 80% of the top websites leak user searches to advertisersSecurity researchers at Norton Labs have found that roughly eight out of ten websites featuring a...
Cloud attacks on the supply chain are a huge concern
Cloud attacks on the supply chain are a huge concernContenido de la entradaLeer másProofpoint News Feed
iPhone 14 cheat sheet: Everything to know about Apple’s 2022 flagship phones
iPhone 14 cheat sheet: Everything to know about Apple’s 2022 flagship phonesLearn all about the key features, specs, pricing, availability and other details about Apple's 2022...
Cybercrime Group TA558 Ramps Up Email Attacks Against Hotels
Cybercrime Group TA558 Ramps Up Email Attacks Against HotelsContenido de la entradaLeer másProofpoint News Feed
Microsoft: Iranian hackers encrypt Windows systems using BitLocker
Microsoft: Iranian hackers encrypt Windows systems using BitLockerMicrosoft says an Iranian state-sponsored threat group it tracks as DEV-0270 (aka Nemesis Kitten) has been abusing the BitLocker...
PCI DSS compliance improving but still lags highs
PCI DSS compliance improving but still lags highsThe new PCI DSS 4.0 standard means organizations will have to up their game beginning in 2024. The post...
Cloud security: Increased concern about risks from partners, suppliers
Cloud security: Increased concern about risks from partners, suppliersContenido de la entradaLeer másProofpoint News Feed
How Malicious Actors Abuse Native Linux Tools in Attacks
How Malicious Actors Abuse Native Linux Tools in AttacksThrough our honeypots and telemetry, we were able to observe instances in which malicious actors abused native Linux...
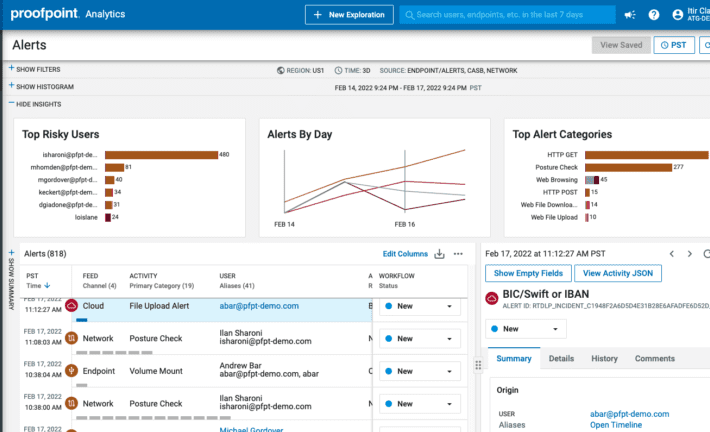
Best Data Security Solution | Proofpoint Information Protection
Best Data Security Solution | Proofpoint Information ProtectionContenido de la entradaLeer másProofpoint News Feed
Microsoft rolls out emergency fix for blocked Windows logins
Microsoft rolls out emergency fix for blocked Windows loginsMicrosoft says a Windows 11 update released in late August is blocking customers from signing in with newly added...
How to manage ad blocking in Opera
How to manage ad blocking in OperaJack Wallen shows you how to take control of online advertisements in the Opera web browser, so you can stop...
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance Platform
Proofpoint Introduces a Smarter Way to Stay Compliant with New Intelligent Compliance PlatformContenido de la entradaLeer másProofpoint News Feed
Chinese hackers tied to attacks on South China Sea energy firms
Chinese hackers tied to attacks on South China Sea energy firmsContenido de la entradaLeer másProofpoint News Feed
Warning of ransomware attacks on schools, here’s how to prepare…
Warning of ransomware attacks on schools, here’s how to prepare…EXECUTIVE SUMMARY: Earlier today, US agencies released a joint advisory pertaining to ransomware attacks on American schools....
US recovers $30 million stolen from Axie Infinity by Lazarus hackers
US recovers $30 million stolen from Axie Infinity by Lazarus hackersWith the help of blockchain analysts and FBI agents, the U.S. government seized $30 million worth...
SilentHound – Quietly Enumerate An Active Directory Domain Via LDAP Parsing Users, Admins, Groups, Etc.
SilentHound – Quietly Enumerate An Active Directory Domain Via LDAP Parsing Users, Admins, Groups, Etc.Quietly enumerate an Active Directory Domain via LDAP parsing users, admins, groups,...
ESP32 Marauder v0.9.12 releases: suite of WiFi/Bluetooth offensive and defensive tools for the ESP32
ESP32 Marauder v0.9.12 releases: suite of WiFi/Bluetooth offensive and defensive tools for the ESP32ESP32 Marauder The ESP32 Marauder is a suite of WiFi/Bluetooth offensive and defensive...
Chinese hackers target energy sector in Australia, South China Sea
Chinese hackers target energy sector in Australia, South China SeaContenido de la entradaLeer másProofpoint News Feed
Three Sentenced in the UK for Selling Drugs on the Darkweb
Three Sentenced in the UK for Selling Drugs on the DarkwebThree drug dealers were sentenced to prison for producing and selling kilogram quantities of drugs on...
CVE-2022-29154: Rsync client-side arbitrary file write vulnerability
CVE-2022-29154: Rsync client-side arbitrary file write vulnerabilityThe developer of the rsync project has just released new versions of their software to patch a vulnerability (CVE-2022-29154) that......
ForceAdmin: Create infinite UAC prompts forcing a user to run as admin
ForceAdmin: Create infinite UAC prompts forcing a user to run as adminForceAdmin ForceAdmin is a c# payload builder, creating infinite UAC pop-ups until the user allows...
Woman Heads to Prison for Hiring a "Hitman” on the Darkweb
Woman Heads to Prison for Hiring a "Hitman” on the DarkwebA Pelahatchie, Mississippi, woman will spend ten years in prison for trying to hire a hitman...
Security Scorecards v4.5 releases: OSS Security Scorecards
Security Scorecards v4.5 releases: OSS Security ScorecardsSecurity Scorecards Goals Automate analysis and trust decisions on the security posture of open source projects. Use this data to......
Apache Tomcat Scanner: scan for Apache Tomcat server vulnerabilities
Apache Tomcat Scanner: scan for Apache Tomcat server vulnerabilitiesApache Tomcat Scanner A python script to scan for Apache Tomcat server vulnerabilities. Features Multithreaded workers to search...
14 ways to secure business data, in layman’s language
14 ways to secure business data, in layman’s languageMazhar Hamayun is a cyber security professional with over 20 years of hands-on technology and leadership experience. At...
Kage – Graphical User Interface For Metasploit Meterpreter And Session Handler
Kage – Graphical User Interface For Metasploit Meterpreter And Session HandlerKage (ka-geh) is a tool inspired by AhMyth designed for Metasploit RPC Server to interact with...
Jersey Teen Sentenced for Buying Amphetamine on Darkweb
Jersey Teen Sentenced for Buying Amphetamine on DarkwebA teenager who bought drugs on the darkweb was given 150 hours of community service. A Jersey teenager who...