Cyberattacks, ransomware incidents expected to rise in 2023Contenido de la entradaLeer másProofpoint News Feed
Month: December 2022
Top AWS cloud security tips to secure your environment
Top AWS cloud security tips to secure your environmentEXECUTIVE SUMMARY: Remember when CodeSpaces was forced out of business within 12 hours after attackers compromised their AWS...
New Python malware backdoors VMware ESXi servers for remote access
New Python malware backdoors VMware ESXi servers for remote accessA previously undocumented Python backdoor targeting VMware ESXi servers has been spotted, enabling hackers to execute commands...
How to boost healthcare cyber security in 2023
How to boost healthcare cyber security in 2023Contributed by George Mack, Content Marketing Manager, Check Point Software. Hackers have made healthcare a top target. As a...
Q&A with Lucia Milică, vice president and global resident CISO at Proofpoint
Q&A with Lucia Milică, vice president and global resident CISO at ProofpointContenido de la entradaLeer másProofpoint News Feed
25+ cyber security experts, driving the security conversation…
25+ cyber security experts, driving the security conversation…EXECUTIVE SUMMARY: In cyber security, change is always coming. The question is, are you ready? This year, CyberTalk.org asked...
Systemic Risk Threatens Every Organization
Systemic Risk Threatens Every OrganizationContenido de la entradaLeer másProofpoint News Feed
Perspectives from the field: Optimizing your cloud security
Perspectives from the field: Optimizing your cloud securityKonstantina Koukou is a well-rounded, tech-savvy electrical engineering graduate with a specialization in Information and Telecommunication Systems and has...
Proofpoint Signs Definitive Agreement to Acquire Illusive
Proofpoint Signs Definitive Agreement to Acquire IllusiveContenido de la entradaLeer másProofpoint News Feed
Is cloud native security good enough?
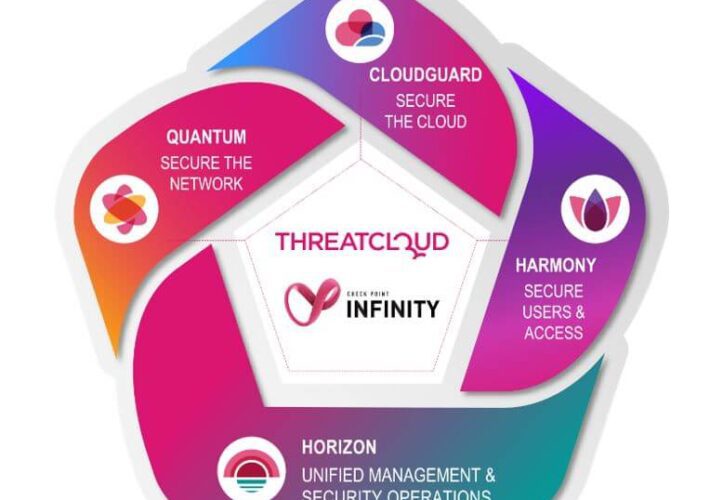
Is cloud native security good enough?By Deryck Mitchelson, Field CISO EMEA, Check Point Software Technologies. Global organizations are digitally transforming via cloud native applications and services....
Artificial intelligence driving high-performance cloud security transformations
Artificial intelligence driving high-performance cloud security transformationsEXECUTIVE SUMMARY: Migrating to the cloud can afford organizations a broad range of new opportunities and can confer numerous business...
K24359631: Intel BIOS firmware vulnerability CVE-2022-21198
K24359631: Intel BIOS firmware vulnerability CVE-2022-21198Intel BIOS firmware vulnerability CVE-2022-21198 Security Advisory Security Advisory Description Time-of-check time-of-use race condition in the BIOS firmware for some Intel(R)...
MY TAKE: The role of semiconductors in bringing the ‘Internet of Everything’ into full fruition
MY TAKE: The role of semiconductors in bringing the ‘Internet of Everything’ into full fruitionThe Internet of Everything (IoE) is on the near horizon. Related: Raising...
GUEST ESSAY: Here’s how and why ‘trust’ presents an existential threat to cybersecurity
GUEST ESSAY: Here’s how and why ‘trust’ presents an existential threat to cybersecurityOver the years, bad actors have started getting more creative with their methods of...
Previewing Black Hat Europe 2022 in London: 12 Hot Sessions
Previewing Black Hat Europe 2022 in London: 12 Hot SessionsCollective DDoS Defense, Rethinking Internet Defense, Zero-Day Harvesting and MoreBlack Hat Europe returns to London, offering deep...
Apple announces new security and privacy measures amid surge in cyber-attacks
Apple announces new security and privacy measures amid surge in cyber-attacksEncryption of iCloud storage means the information will be safeguarded from hackers as well as government...
Clare O’Neil warns counter-terror laws may need to change to better handle rightwing extremism
Clare O’Neil warns counter-terror laws may need to change to better handle rightwing extremismHome affairs minister says government preparing program to counter foreign interference and youth...
A Plan to Address Future Healthcare Cyber Challenges
A Plan to Address Future Healthcare Cyber ChallengesThe Health Sector Coordinating Council is embarking on a five-year strategic plan to help the healthcare and public health...
3 Software Supply Chain Security Pitfalls and How to Avoid Them
3 Software Supply Chain Security Pitfalls and How to Avoid ThemContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Ransomware Defense: Common Mistakes to Avoid
Ransomware Defense: Common Mistakes to AvoidThis week's edition of the ISMG Security Report discusses the mistakes enterprises commonly make when building ransomware defenses, the cybersecurity capabilities...
A Look into Cybercrime and the People Behind It with Brian Krebs
A Look into Cybercrime and the People Behind It with Brian KrebsContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Live Webinar | A Master Class on Cybersecurity: Roger Grimes Teaches Password Best Practices
Live Webinar | A Master Class on Cybersecurity: Roger Grimes Teaches Password Best PracticesContenido de la entradaLeer másDataBreachToday.com RSS Syndication
LIVE Webinar | Native Database Protection Is Not Enough
LIVE Webinar | Native Database Protection Is Not EnoughContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Australian Telecom Firm Leaks Data of 130,000 Customers
Australian Telecom Firm Leaks Data of 130,000 Customers'We're Sorry It Occurred, and We Know We Have Let You Down,' Telstra CFO SaysAustralian telecommunications provider Telstra apologized...
Royal Ransomware Hitting Healthcare Targets and Dumping Data
Royal Ransomware Hitting Healthcare Targets and Dumping DataTongue-in-Cheek Ransom Note Claims 'Modest Royalty' for 'Pentesting Services'Attackers wielding Royal ransomware have been hitting crypto-locking healthcare targets, the...
Microsoft alerta a la industria de criptomonedas sobre ciberataques dirigidos
Microsoft alerta a la industria de criptomonedas sobre ciberataques dirigidosLas empresas de inversión en criptomonedas son el objetivo de un grupo de amenazas en desarrollo que...
Proofpoint to Buy Deception Firm Illusive, Boost Offerings
Proofpoint to Buy Deception Firm Illusive, Boost OfferingsAshan Willy's First Deal as CEO Gets Proofpoint Into the Identity, Deception SpacesAshan Willy has made his first deal...
Investigadores descubren que el nuevo malware Drokbk utiliza GitHub como un solucionador de Dead Drop
Investigadores descubren que el nuevo malware Drokbk utiliza GitHub como un solucionador de Dead DropSe ha atribuido al subgrupo de un grupo de estado-nación iraní conocido...
COVID-bit: nuevo canal COVert para filtrar datos de computadoras con espacio de aire
COVID-bit: nuevo canal COVert para filtrar datos de computadoras con espacio de aireUn método de exfiltración de datos no convencional aprovecha un canal encubierto previamente no...
Mantenga a raya a su Grinch: así es como mantenerse seguro en línea esta temporada navideña
Mantenga a raya a su Grinch: así es como mantenerse seguro en línea esta temporada navideñaA medida que se acerca la temporada navideña, las compras en...