Security Requirements as an Engineering ChallengeBy Milica D. Djekic Independent researcher, Subotica, The Republic of Serbia Abstract Engineering challenges have appeared throughout time […] The post...
Month: December 2022
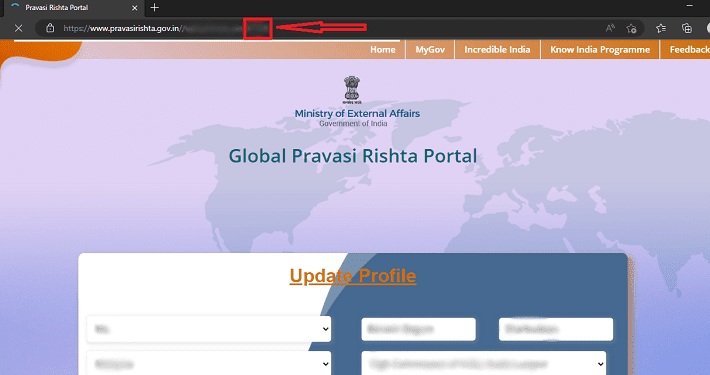
Indian foreign ministry’s Global Pravasi Rishta portal leaks expat passport details
Indian foreign ministry’s Global Pravasi Rishta portal leaks expat passport detailsThe Cybernews research team reported that India’s government platform Global Pravasi Rishta Portal was leaking sensitive...
AI for Cyber Threat Intelligence – Challenges and Mitigation Approaches
AI for Cyber Threat Intelligence – Challenges and Mitigation ApproachesBy Uday Kiran Pulleti, Senior Director – AI, Cyble The internet as we know it is a...
MuddyWater Threat Group Behind Email Phishing Attacks
MuddyWater Threat Group Behind Email Phishing AttacksA malicious group associated to Iran’s Ministry of Intelligence and Security (MOIS), MuddyWater, was reported responsible for delivering phishing messages...
Typosquatting Explained: Definition, Threats, and Safety Tips
Typosquatting Explained: Definition, Threats, and Safety TipsCybercriminals pray on our online mistakes, learning how to transform them into money better and faster. And one of the...
Clop Ransomware Uses Viral ‘Truebot’ Malware to Access Networks
Clop Ransomware Uses Viral ‘Truebot’ Malware to Access NetworksSecurity researchers recently noticed a surge in new devices infected with the Truebot malware downloader. This is created...
SMB Cyber Insurance: The End of Innocence
SMB Cyber Insurance: The End of InnocenceBy Nadav Arbel, Co-Founder & CEO, CYREBRO The cyber insurance landscape has changed dramatically in recent years – […] The...
Ransomware 101: What Is Targeted Ransomware and How Does It Work
Ransomware 101: What Is Targeted Ransomware and How Does It WorkTo understand what targeted ransomware is and to know the difference between opportunistic and targeted ransomware,...
Cloud Patch Management Explained: What Is It and Why Is It Important?
Cloud Patch Management Explained: What Is It and Why Is It Important?Cloud patch management is one of the most important and often overlooked, aspects of cloud...
Unpatched Vulnerabilities Cause Pulse Connect Secure Hosts to Be at Risk
Unpatched Vulnerabilities Cause Pulse Connect Secure Hosts to Be at RiskResearchers have found more than 4,000 vulnerable Pulse Connect Secure hosts being exposed to the internet....
Data Breach Gives Threat Actors Complete Information about Vevor Clients
Data Breach Gives Threat Actors Complete Information about Vevor ClientsA multi-terabyte database belonging to Vevor was left open to the public this year starting July 12th...
Rackspace Warns Clients About Phishing Risks After Suffering a Ransomware Attack
Rackspace Warns Clients About Phishing Risks After Suffering a Ransomware AttackFollowing a ransomware attack that affected its hosted Microsoft Exchange environment, cloud computing firm Rackspace issued...
The Art and Science of Building a Cyber Security Tech Stack
The Art and Science of Building a Cyber Security Tech StackHow companies should approach assessing risk and vulnerabilities and build cybersecurity tech stacks that address their...
COVID-bit: A New Attack Method That Can Breach Air-gapped PCs
COVID-bit: A New Attack Method That Can Breach Air-gapped PCsCOVID-bit is a new assault strategy that uses electromagnetic waves to breach air-gapped computers, and it has...
The Data Problem
The Data ProblemToday, data is essential to companies’ success, yet, at the same time, it is incumbent on them to […] The post The Data Problem...
Man Arrested for Hacking NY Hair Salon’s POS Provider and Stealing $400K
Man Arrested for Hacking NY Hair Salon’s POS Provider and Stealing $400KA man from Arizona was detained and charged for hacking into a hair salon chain...
The Remote Workforce is Here to Stay
The Remote Workforce is Here to StayHow this Impacts Security By Metin Kortak, Chief Information Security Officer, Rhymetec As the post-pandemic business recovery continues, […] The...
AppleJeus Malware Detection: North Korea-Linked Lazarus APT Spreads Malicious Strains Masquerading as Cryptocurrency Apps
AppleJeus Malware Detection: North Korea-Linked Lazarus APT Spreads Malicious Strains Masquerading as Cryptocurrency Apps A notorious North Korea-backed APT group, Lazarus, continuously broadens its attack surface,...
DolphinCape Malware Detection: Phishing Campaign Against Ukrainian Railway Transport Organization of Ukraine “Ukrzaliznytsia” Related to the Use of Iranian Shahed-136 Drones
DolphinCape Malware Detection: Phishing Campaign Against Ukrainian Railway Transport Organization of Ukraine “Ukrzaliznytsia” Related to the Use of Iranian Shahed-136 Drones Since the outbreak of the...
North Korean hackers exploit Seoul Halloween tragedy in zero-day attack
North Korean hackers exploit Seoul Halloween tragedy in zero-day attackMalicious hackers, hell-bent on infiltrating an organisation, have no qualms about exploiting even the most tragic events....
Smashing Security podcast #301: AI chatbot or the start of Skynet? Eufy privacy, and hot desks
Smashing Security podcast #301: AI chatbot or the start of Skynet? Eufy privacy, and hot desksAn AI chatbot is causing a stir - both impressing and...
Metaparasites: The cybercriminals who rip each other off
Metaparasites: The cybercriminals who rip each other offResearchers at Sophos have investigated so-called "metaparasites" - the scammers who scam other scammers.Leer másGraham CluleyResearchers at Sophos have...
Hive ransomware gang claims responsibility for attack on Intersport that left cash registers disabled
Hive ransomware gang claims responsibility for attack on Intersport that left cash registers disabledSports retail giant Intersport, which boasts some 6000 stores worldwide in 57 countries,...
Rackspace customers rage following ransomware attack, as class-action lawsuits filed
Rackspace customers rage following ransomware attack, as class-action lawsuits filedAs ever, what matters most is not so much whether an organisation gets hit or not by...
CryWiper Data Wiper Targeting Russian Sites
CryWiper Data Wiper Targeting Russian SitesKaspersky is reporting on a data wiper masquerading as ransomware that is targeting local Russian government networks. The Trojan corrupts any...
Security Vulnerabilities in Eufy Cameras
Security Vulnerabilities in Eufy CamerasEufy cameras claim to be local only, but upload data to the cloud. The company is basically lying to reporters, despite being...
Leaked Signing Keys Are Being Used to Sign Malware
Leaked Signing Keys Are Being Used to Sign MalwareA bunch of Android OEM signing keys have been leaked or stolen, and they are actively being used...
The Decoupling Principle
The Decoupling PrincipleThis is a really interesting paper that discusses what the authors call the Decoupling Principle: The idea is simple, yet previously not clearly articulated:...
Friday Squid Blogging: China Bans Taiwanese Squid Imports
Friday Squid Blogging: China Bans Taiwanese Squid ImportsToday I have some squid geopolitical news. As usual, you can also use this squid post to talk about...
Hacking Trespass Law
Hacking Trespass LawThis article talks about public land in the US that is completely surrounded by private land, which in some cases makes it inaccessible to...