Google unveils beta of client-side encryption for GmailCustomers of Google Workspace Enterprise Plus, Education Plus, or Education Standard can apply for the beta until Jan. 20,...
Month: December 2022
Know Yourself, Know your Enemy: Diversity means Security
Know Yourself, Know your Enemy: Diversity means SecurityCovid-19 has created a new urgency for cyber security solutions in Asia By Nora Cao, Director of Cyber […]...
On-premises vs cloud security: What are the pros and cons?
On-premises vs cloud security: What are the pros and cons?Is on-premises or cloud computing operations more secure for your business? Consider the security pros and cons...
What is Microsoft’s Secure Supply Chain Consumption Framework, and why should I use it?
What is Microsoft’s Secure Supply Chain Consumption Framework, and why should I use it?Microsoft has open sourced its framework for managing open source in software development....
Conti Team One Splinter Group Resurfaces as Royal Ransomware with Callback Phishing Attacks
Conti Team One Splinter Group Resurfaces as Royal Ransomware with Callback Phishing AttacksFrom September to December, we detected multiple attacks from the Royal ransomware group. In...
GodFather Android Banking Trojan Targeting Users of Over 400 Banking and Crypto Apps
GodFather Android Banking Trojan Targeting Users of Over 400 Banking and Crypto AppsAn Android banking trojan known as GodFather is being used to target users of more than...
Turbocharge your IT career with this cybersecurity skills training for only $50
Turbocharge your IT career with this cybersecurity skills training for only $50Whether you've been in IT for two, five or 10 years, this e-learning bundle can...
If Cyber Literacy Is The New Financial Literacy, Then The Equation Must Add Up
If Cyber Literacy Is The New Financial Literacy, Then The Equation Must Add UpBy Colm Murphy, Senior Cyber Security Advisor, Huawei If you are a member...
Study to ace five cybersecurity certification exams
Study to ace five cybersecurity certification examsDive into CompTIA, NIST, CISSP and more with the online training offered in The 2022 Ultimate Advanced CyberSecurity Professional Certification...
Hacked Ring Cams Used to Record Swatting Victims
Hacked Ring Cams Used to Record Swatting Victims Photo: BrandonKleinPhoto / Shutterstock.com Two U.S. men have been charged with hacking into the Ring home security cameras...
Microsoft shares details for a Gatekeeper Bypass bug in Apple macOS
Microsoft shares details for a Gatekeeper Bypass bug in Apple macOSMicrosoft disclosed technical details of a vulnerability in Apple macOS that could be exploited by an...
Three Lessons from A Unit 8200 Cybersecurity Alum
Three Lessons from A Unit 8200 Cybersecurity AlumBy Yotam Segev, Co-Founder and CEO, Cyera The cybersecurity startup community continues to be dominated by former Israeli […]...
Russia-linked Gamaredon APT targeted a petroleum refining company in a NATO nation in August
Russia-linked Gamaredon APT targeted a petroleum refining company in a NATO nation in AugustRussia-linked Gamaredon APT group targeted a large petroleum refining company in a NATO...
Three Steps Towards a More Secure OT Infrastructure
Three Steps Towards a More Secure OT InfrastructureBy Jason Weber, Vice President of Product, Veracity Industrial Networks Years ago, the biggest concern from the plant […]...
The Best Way To Protect Your Online Identity
The Best Way To Protect Your Online Identity For many Aussies, identity theft was always something that happened to other people. People on TV, usually. But...
Impact of cloud configuration security practices
Impact of cloud configuration security practicesCloud configuration security practices are important to prevent cyber threats.Leer másArticles RSS FeedCloud configuration security practices are important to prevent cyber...
Operation Power Off: 50 DDoS-services taken offline in international crackdown
Operation Power Off: 50 DDoS-services taken offline in international crackdownLaw enforcement agencies in the United States, UK, Netherlands, Poland, and Germany have brought down the most...
Smashing Security podcast #302: Lensa AI, and a dog called Bob
Smashing Security podcast #302: Lensa AI, and a dog called BobDrug dealers come unstuck while using the Encrochat encrypted-messaging app, and we put the Lensa AI’s...
Trojaned Windows Installer Targets Ukraine
Trojaned Windows Installer Targets UkraineMandiant is reporting on a trojaned Windows installer that targets Ukrainian users. The installer was left on various torrent sites, presumably ensnaring...
Backup saves the day after crime author loses laptop in blizzard
Backup saves the day after crime author loses laptop in blizzardCelebrated crime author Ann Cleeves turned to Twitter this week, desperate for help. The reason? The...
Microsoft approved and digitally-signed malicious drivers used in ransomware attacks
Microsoft approved and digitally-signed malicious drivers used in ransomware attacksMicrosoft has warned that malicious hackers were able to get the software giant to digitally sign their...
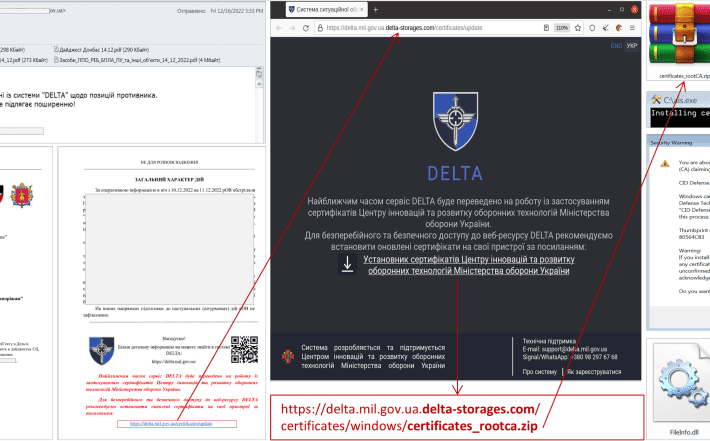
UAC-0142 APT targets Ukraine’s Delta military intelligence program
UAC-0142 APT targets Ukraine’s Delta military intelligence programUkraine’s CERT-UA revealed the national Delta military intelligence program has been targeted with a malware-based attack. On December 17,...
To Secure the Software Supply Chain, Start with a SBOM
To Secure the Software Supply Chain, Start with a SBOMHaving a SBOM can reduce the “fog of war” and enable businesses to assess risk and impact...
Ukraine Intercepting Russian Soldiers’ Cell Phone Calls
Ukraine Intercepting Russian Soldiers’ Cell Phone CallsThey’re using commercial phones, which go through the Ukrainian telecom network: “You still have a lot of soldiers bringing cellphones...
Data breach at Social Blade confirmed. Hacker offers to sell database on underground website
Data breach at Social Blade confirmed. Hacker offers to sell database on underground websiteSocial media analytics service Social Blade has confirmed that it is investigating a...
3 Trends Shaping the Future Of Attack Surface Management
3 Trends Shaping the Future Of Attack Surface ManagementBy David Monnier, Team Cymru Fellow Will your organization become the next big cyberattack reported in the news?...
Critical Microsoft Code-Execution Vulnerability
Critical Microsoft Code-Execution VulnerabilityA critical code-execution vulnerability in Microsoft Windows was patched in September. It seems that researchers just realized how serious it was (and is):...
FateGrab/StealDeal Detection: Phishing Attacks by the UAC-0142 Group Against Ukrainian Government Entities Targeting DELTA Users
FateGrab/StealDeal Detection: Phishing Attacks by the UAC-0142 Group Against Ukrainian Government Entities Targeting DELTA Users Phishing attacks on Ukrainian state bodies spreading diverse malware strains have...
Smashing Security podcast #303: Secret Roomba snaps, Christmas cab scams, and the future of AI
Smashing Security podcast #303: Secret Roomba snaps, Christmas cab scams, and the future of AIBeware your Roomba's roving eye, the Finns warn of AI threats around...
A Local Solution to A Global Problem: Why Cyber Security Operation Centres Should Be UK Based
A Local Solution to A Global Problem: Why Cyber Security Operation Centres Should Be UK BasedWhere you choose to base your SOC physically is a crucial...