Weekly Update 319Geez we've been getting hammered down here: Optus, MyDeal, Vinomofo, Medibank and now Australian Clinical Labs. It's crazy how much press interest there's been...
Month: October 2022
Largest EU copper producer Aurubis suffers cyberattack, IT outage
Largest EU copper producer Aurubis suffers cyberattack, IT outageGerman copper producer Aurubis has announced that it suffered a cyberattack that forced it to shut down IT...
Single chip transfers the entire internet’s traffic in a second
Single chip transfers the entire internet’s traffic in a secondEXECUTIVE SUMMARY: A single chip has managed a transfer of over a petabit-per-second, according to new research...
Friday Squid Blogging: Chinese Squid Fishing
Friday Squid Blogging: Chinese Squid FishingChina claims that it is “engaging in responsible squid fishing”: Chen Xinjun, dean of the College of Marine Sciences at Shanghai...
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedIn
Battle with Bots Prompts Mass Purge of Amazon, Apple Employee Accounts on LinkedInOn October 10, 2022, there were 576,562 LinkedIn accounts that listed their current employer...
5 Ways to Protect Your Online Privacy
5 Ways to Protect Your Online Privacy When you open your laptop or your mobile device, what is the first thing you do? Do you head to...
Microsoft shares workaround for ongoing Outlook login issues
Microsoft shares workaround for ongoing Outlook login issuesMicrosoft is working on a fix for ongoing sign-in issues affecting some Outlook for Microsoft 365 customers and preventing them...
Cranefly uses new communication technique in attack campaigns
Cranefly uses new communication technique in attack campaignsA threat actor dubbed "Cranefly" uses a new technique for its communications on infected targets. The post Cranefly uses...
Why Employers Should Embrace Competency-Based Learning in Cybersecurity
Why Employers Should Embrace Competency-Based Learning in CybersecurityThere is a growing movement toward increasing the use of competency and skills-based education and hiring practices in both...
Hijacked New York Post Site Highlights the ‘Insider Threat’ — Again
Hijacked New York Post Site Highlights the 'Insider Threat' -- AgainContenido de la entradaLeer másProofpoint News Feed
K44030142: OpenSSL vulnerability – Pending Critical Disclosure (November 1)
K44030142: OpenSSL vulnerability - Pending Critical Disclosure (November 1)OpenSSL vulnerability - Pending Critical Disclosure (November 1) Security Advisory Security Advisory Description The OpenSSL organization will release...
Cybercrime in Australia has been on the rise for years, but Optus and Medibank have been wake-up calls
Cybercrime in Australia has been on the rise for years, but Optus and Medibank have been wake-up callsExperts say the recent prominence of data breaches is...
K44030142: OpenSSL vulnerability – Pending Critical Disclosure (November 1)
K44030142: OpenSSL vulnerability - Pending Critical Disclosure (November 1)OpenSSL vulnerability - Pending Critical Disclosure (November 1) Security Advisory Security Advisory Description The OpenSSL organization will release...
K44030142: OpenSSL vulnerability – Pending Critical Disclosure (November 1)
K44030142: OpenSSL vulnerability - Pending Critical Disclosure (November 1)OpenSSL vulnerability - Pending Critical Disclosure (November 1) Security Advisory Security Advisory Description The OpenSSL organization will release...
Cyber Events Disrupt Polish, Slovakian Parliament IT Systems
Cyber Events Disrupt Polish, Slovakian Parliament IT SystemsPoland Senate Alleges Russian Connection to DDoS AttackParliament IT systems in two East European capitals were disrupted Thursday. The...
Fallout From Medibank Hack Grows
Fallout From Medibank Hack GrowsAbout 4M Australians Affected by Extortion Demand Made Against the Health InsurerFallout from the hack of Australian health insurer Medibank continues to...
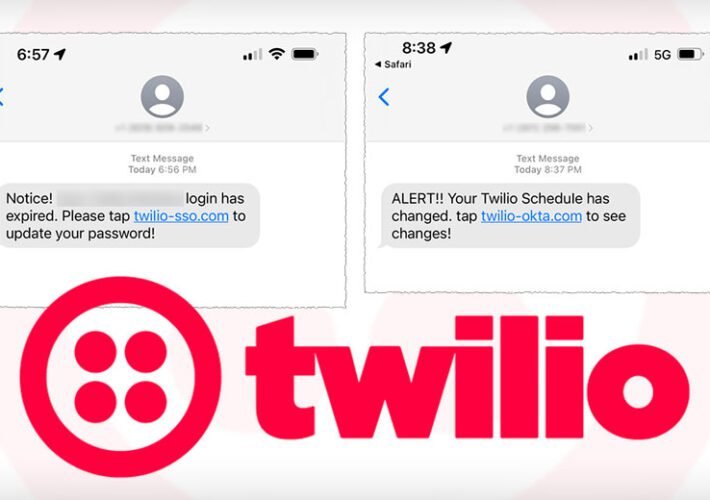
Final Twilio Smishing Victim Count Reaches 209
Final Twilio Smishing Victim Count Reaches 209Same 0ktapus Hackers Likely Also Responsible for Earlier BreachCustomer engagement platform Twilio says the number of customers affected by a...
What the Uber verdict means to CISOs: You’re (probably) not going to jail
What the Uber verdict means to CISOs: You're (probably) not going to jailThere seem to be two reactions to the verdict in the Sullivan case. One...
New Chinese attack framework Alchimist serves Windows, Linux, and macOS implants
New Chinese attack framework Alchimist serves Windows, Linux, and macOS implantsResearchers have discovered a new attack framework of Chinese origin that they believe is being used...
Top skill-building resources and advice for CISOs
Top skill-building resources and advice for CISOsThe role of the CISO has evolved, and so have the responsibilities. Some believe a CISO must have technical knowledge...
BrandPost: Why Ease-of-Use is Central to Better Security
BrandPost: Why Ease-of-Use is Central to Better SecurityHere is an old joke from my days as a consultant. A customer asked, “How can I be sure...
Altruism under attack: why cybersecurity has become essential to humanitarian nonprofits
Altruism under attack: why cybersecurity has become essential to humanitarian nonprofitsHumanitarian initiatives have always been of huge global importance, but perhaps never more so than over...
8 top multi-factor authentication products and how to choose an MFA solution
8 top multi-factor authentication products and how to choose an MFA solutionToday’s credential-based attacks are much more sophisticated. Whether it’s advanced phishing techniques, credential stuffing, or...
Supply chain attacks increased over 600% this year and companies are falling behind
Supply chain attacks increased over 600% this year and companies are falling behindThe number of documented supply chain attacks involving malicious third-party components has increased 633%...
High, medium severity vulnerabilities impacting Zimbra Collaboration Suite
High, medium severity vulnerabilities impacting Zimbra Collaboration SuiteThreat actors are actively exploiting multiple Common Vulnerabilities and Exposures (CVEs) against enterprise cloud-hosted collaboration software and email platform...
Attackers switch to self-extracting password-protected archives to distribute email malware
Attackers switch to self-extracting password-protected archives to distribute email malwareDistributing malware inside password-protected archives has long been one of the main techniques used by attackers to...
Financial losses to synthetic identity-based fraud to double by 2024
Financial losses to synthetic identity-based fraud to double by 2024Losses to imposter scams based on synthetic identities—identities that only exist as figments in a credit reporting...
Securing your organization against phishing can cost up to $85 per email
Securing your organization against phishing can cost up to $85 per emailAs phishing attacks increase, preventing them from doing damage is proving costly for organizations. Phishing-related...
With Conti gone, LockBit takes lead of the ransomware threat landscape
With Conti gone, LockBit takes lead of the ransomware threat landscapeThe number of ransomware attacks observed over the previous three months declined compared to the previous...
96% of companies report insufficient security for sensitive cloud data
96% of companies report insufficient security for sensitive cloud dataThe vast majority of organizations lack confidence in securing their data in cloud, while many companies acknowledge...