Evil Corp and Conti Linked to Cisco Data Breach, eSentire SuggestsThe firm said the tools used to attack Cisco were also deployed to compromise one of...
Month: September 2022
Golang-based Malware Campaign Relies on James Webb Telescope’s Image
Golang-based Malware Campaign Relies on James Webb Telescope's ImageInitial infection begins with a phishing email containing a Microsoft Office attachmentLeer másInitial infection begins with a phishing...
Microsoft Finds Account Takeover Bug in TikTok
Microsoft Finds Account Takeover Bug in TikTokVulnerability impacted social media firm’s Android appLeer másVulnerability impacted social media firm’s Android app
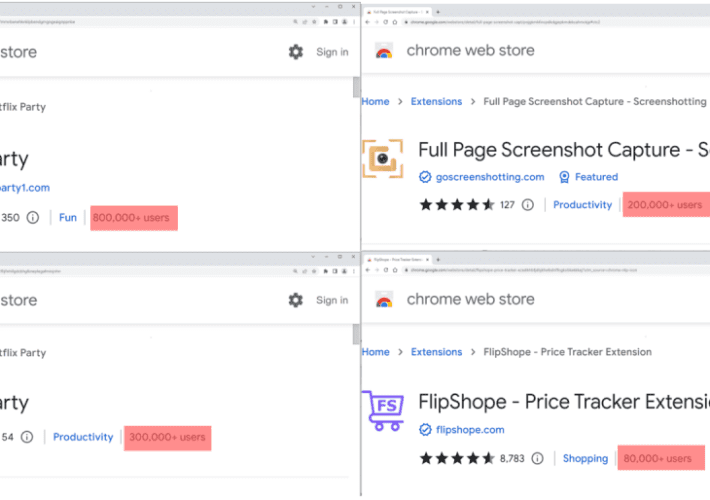
Experts spotted five malicious Google Chrome extensions used by 1.4M users
Experts spotted five malicious Google Chrome extensions used by 1.4M usersResearchers spotted 5 malicious Google Chrome extensions used to track users’ browsing activity and profit of...
Threat actors breached the network of the Italian oil company ENI
Threat actors breached the network of the Italian oil company ENIItalian oil giant Eni was hit by a cyber attack, attackers compromised its computer networks, but...
GO#WEBBFUSCATOR campaign hides malware in NASA’s James Webb Space Telescope image
GO#WEBBFUSCATOR campaign hides malware in NASA’s James Webb Space Telescope imageA malware campaign tracked as GO#WEBBFUSCATOR used an image taken from NASA’s James Webb Space Telescope...
Detected Cyber-Threats Surge 52% in 1H 2022
Detected Cyber-Threats Surge 52% in 1H 2022Trend Micro warns of Linux-based ransomwareLeer másTrend Micro warns of Linux-based ransomware
How to take control over your digital legacy
How to take control over your digital legacyDo you have a plan for what will happen to your digital self when you pass away? Here’s how...
Standards Body Publishes Guidelines for IoT Security Testing
Standards Body Publishes Guidelines for IoT Security TestingDocument will help testers create benchmarks for security productsLeer másDocument will help testers create benchmarks for security products
A flaw in TikTok Android app could have allowed the hijacking of users’ accounts
A flaw in TikTok Android app could have allowed the hijacking of users’ accountsMicrosoft discovered a vulnerability in the TikTok app for Android that could lead...
FBI is helping Montenegro in investigating the ongoing cyberattack
FBI is helping Montenegro in investigating the ongoing cyberattackA team of cybersecurity experts from the US FBI will help the authorities in Montenegro to investigate the...
Apple released patches for recently disclosed WebKit zero-day in older iPhones and iPads
Apple released patches for recently disclosed WebKit zero-day in older iPhones and iPadsApple released new security updates for older iPhone and iPad devices addressing recently fixed WebKit...
START Confirms Data Breach
START Confirms Data BreachSTART (start.ru), a Russian media streaming platform, has confirmed the rumors that emerged on Sunday, August 28, about a data breach. The cybercriminals...
Genshin Impact Ransomware Infection: Adversaries Abuse the Anti-Cheat Driver
Genshin Impact Ransomware Infection: Adversaries Abuse the Anti-Cheat Driver Genshin Impact, a popular open-world action RPG, is leveraged to spread ransomware. Threat actors abuse mhyprot2.sys, a...
Smashing Security podcast #287: Lost in translation, spiders, and slapping tortillas
Smashing Security podcast #287: Lost in translation, spiders, and slapping tortillasWe’re back from our summer break as we ask how did a cryptomining campaign stay unspotted...
Final Thoughts on Ubiquiti
Final Thoughts on UbiquitiLast year, I posted a series of articles about a purported “breach” at Ubiquiti. My sole source for that reporting was the person...
Aussies Fear Snakes, Spiders and Getting Hacked
Aussies Fear Snakes, Spiders and Getting Hacked Fears and phobias. We all have them. But what are your biggest ones? I absolutely detest snakes but spiders...
Our Quest: Advancing Product Labels to Help Consumers Consider Cybersecurity
Our Quest: Advancing Product Labels to Help Consumers Consider CybersecurityFor many decades, consumers have relied on labels to help them make decisions about which products to...
Microsoft found TikTok Android flaw that let hackers hijack accounts
Microsoft found TikTok Android flaw that let hackers hijack accountsMicrosoft found and reported a high severity flaw in the TikTok Android app in February that allowed attackers...
Ragnar Locker ransomware claims attack on Portugal’s flag airline
Ragnar Locker ransomware claims attack on Portugal's flag airlineThe Ragnar Locker ransomware gang has claimed an attack on the flag carrier of Portugal, TAP Air Portugal,...
Google Chrome bug lets sites write to clipboard without asking
Google Chrome bug lets sites write to clipboard without askingChrome version 104 accidentally introduced a bug that removes the user requirement to approve clipboard writing events...
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel Sectors
Summertime Blues: TA558 Ramps Up Attacks on Hospitality, Travel SectorsContenido de la entradaLeer másProofpoint News Feed
Why MDR Has Become Integral to Modern Cybersecurity Strategies is a new ESG Showcase Report Available Now
Why MDR Has Become Integral to Modern Cybersecurity Strategies is a new ESG Showcase Report Available NowThreats are multiplying in number and morphing in complexity faster...
Duo Helps Organisations with ACSC Mitigation Strategies
Duo Helps Organisations with ACSC Mitigation StrategiesCyberattacks in Australia continue to rise year after year. Over the 2020-21 financial year, Australia saw a 13% increase in...
AdGuard’s new ad blocker struggles with Google’s Manifest v3 rules
AdGuard’s new ad blocker struggles with Google’s Manifest v3 rulesAdGuard has published the first ad blocker extension for Chrome that is compatible with Manifest V3, Google's...
Securing the Emerging Hybrid Workforce
Securing the Emerging Hybrid WorkforceToday’s working environment has led many organizations to consider adopting a “hybrid workforce” that allows greater flexibility for their employees. For some...
Zero Trust at Scale
Zero Trust at ScaleSince incorporating controls for device health and trust at the application layer, our ability to react to device risk has substantially improved. For...
6 different types of CISOs and the environments they thrive in
6 different types of CISOs and the environments they thrive inEXECUTIVE SUMMARY: The CISO’s role is to protect the business from cyber threats, but often times...
Making Cybersecurity Mesh Architectures a Reality With the Fortinet Security Fabric
Making Cybersecurity Mesh Architectures a Reality With the Fortinet Security FabricThe Fortinet Security Fabric delivers the broad, integrated, and automated capabilities needed to make a cybersecurity...
Why Cyber Security is Creating a Competitive Advantage
Why Cyber Security is Creating a Competitive AdvantageWhen Forbes took a mid-2022 look at the state of global cyber security, one highlighted statistic was a real...