Russian Sandworm APT impersonates Ukrainian telcos to deliver malwareRussia-linked APT group Sandworm has been observed impersonating telecommunication providers to target Ukrainian entities with malware. Russia-linked cyberespionage...
Day: September 22, 2022
Imperva blocked a record DDoS attack with 25.3 billion requests
Imperva blocked a record DDoS attack with 25.3 billion requestsCybersecurity company Imperva announced to have mitigated a distributed denial-of-service (DDoS) attack with a total of over...
350K Open-Source Projects At Risk of Supply Chain Vulnerability
350K Open-Source Projects At Risk of Supply Chain VulnerabilityThe flaw resides in the tarfile module, automatically installed in any Python projectLeer másThe flaw resides in the...
Ransomware is (slightly) on the decline, cyberinsurance company says
Ransomware is (slightly) on the decline, cyberinsurance company saysRansomware attacks began to become both less common and less costly in the first half of 2022, as...
Microsoft Upgrades Windows 11 With New Security Features
Microsoft Upgrades Windows 11 With New Security FeaturesThe list includes application control enhancements and vulnerable drivers protection, among othersLeer másThe list includes application control enhancements and...
Automatic Cheating Detection in Human Racing
Automatic Cheating Detection in Human RacingThis is a fascinating glimpse of the future of automatic cheating detection in sports: Maybe you heard about the truly insane...
U.S. gov adds more Chinese Telecom firms to the Covered List
U.S. gov adds more Chinese Telecom firms to the Covered ListThe U.S. Federal Communications Commission (FCC) has added more Chinese telecom firms to the Covered List....
Hackers stole $160 Million from Crypto market maker Wintermute
Hackers stole $160 Million from Crypto market maker WintermuteThreat actors have stolen around $160 million worth of digital assets worth from crypto trading firm Wintermute. Malicious actors...
Iranian Hackers Hid in Albanian Networks for Over a Year
Iranian Hackers Hid in Albanian Networks for Over a YearCISA report reveals extent of state-backed campaignLeer másCISA report reveals extent of state-backed campaign
Top 5 attack surface challenges related to security operations
Top 5 attack surface challenges related to security operationsAccording to newly published ESG research, just over half of all organizations (52%) say that security operations are...
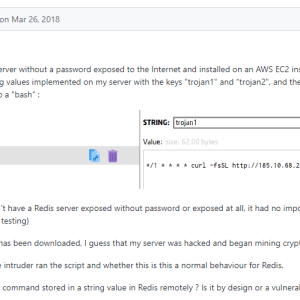
Over 39K unauthenticated Redis services on the internet targeted in cryptocurrency campaign
Over 39K unauthenticated Redis services on the internet targeted in cryptocurrency campaignThreat actors targeted tens thousands of unauthenticated Redis servers exposed on the internet as part...
Why is my Wi‑Fi slow and how do I make it faster?
Why is my Wi‑Fi slow and how do I make it faster?Has your Wi-Fi speed slowed down to a crawl? Here are some of the possible...
A disgruntled developer is the alleged source of the leak of the Lockbit 3.0 builder
A disgruntled developer is the alleged source of the leak of the Lockbit 3.0 builderA disgruntled developer seems to be responsible for the leak of the...
Report: The state of secure identity 2022
Report: The state of secure identity 2022A new report from Okta has found that credential stuffing as a means of breaching Customer Identity and Access Management...
Authorized Push Payments Surge to 75% of Banking Fraud
Authorized Push Payments Surge to 75% of Banking FraudSocial engineering tactics bear fruit for digital scammersLeer másSocial engineering tactics bear fruit for digital scammers
You never walk alone: The SideWalk backdoor gets a Linux variant
You never walk alone: The SideWalk backdoor gets a Linux variantESET researchers have uncovered another tool in the already extensive arsenal of the SparklingGoblin APT group:...
Former Broadcom engineer gets eight months in prison for trade secrets theft
Former Broadcom engineer gets eight months in prison for trade secrets theftPeter Kisang Kim admitted to stealing Broadcom data related to its Trident family of network...
Cisco Event Response: September 2022 Semiannual Cisco IOS XR Software Security Advisory Bundled Publication
Cisco Event Response: September 2022 Semiannual Cisco IOS XR Software Security Advisory Bundled PublicationContenido de la entradaLeer másCisco Event Responses
SparklingGoblin deploys new Linux backdoor – Week in security, special edition
SparklingGoblin deploys new Linux backdoor – Week in security, special editionESET Research first spotted this variant of the SideWalk backdoor in the network of a Hong...
Third‑party cookies: How they work and how to stop them from tracking you across the web
Third‑party cookies: How they work and how to stop them from tracking you across the webCross-site tracking cookies have a bleak future but can still cause...
Rising to the challenges of secure coding – Week in security with Tony Anscombe
Rising to the challenges of secure coding – Week in security with Tony AnscombeThe news seems awash this week with reports of both Microsoft and Apple...
Twitter Password Reset Bug Exposed User Accounts
Twitter Password Reset Bug Exposed User AccountsSocial media firm fixes issue that left sessions openLeer másSocial media firm fixes issue that left sessions open
Multi-factor authentication fatigue attacks are on the rise: How to defend against them
Multi-factor authentication fatigue attacks are on the rise: How to defend against themCredential compromise has been one of the top causes for network security breaches for...
Can your iPhone be hacked? What to know about iOS security
Can your iPhone be hacked? What to know about iOS securityHere are some of the most common ways that an iPhone can be compromised with malware,...
D&O insurance not yet a priority despite criminal trial of Uber’s former CISO
D&O insurance not yet a priority despite criminal trial of Uber’s former CISOThe trial of former Uber CISO Joe Sullivan marks the first time a cybersecurity...
Critical Remote Hack Flaws Found in Dataprobe’s Power Distribution Units
Critical Remote Hack Flaws Found in Dataprobe's Power Distribution UnitsThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday released an industrial control systems (ICS) advisory...
Product Review: Stellar Cyber Open XDR Platform
Product Review: Stellar Cyber Open XDR PlatformAlmost every vendor, from email gateway companies to developers of threat intelligence platforms, is positioning themselves as an XDR player....
Why Zero Trust Should be the Foundation of Your Cybersecurity Ecosystem
Why Zero Trust Should be the Foundation of Your Cybersecurity EcosystemFor cybersecurity professionals, it is a huge challenge to separate the “good guys” from the “villains”....
Serious Security: Browser-in-the-browser attacks – watch out for windows that aren’t!
Serious Security: Browser-in-the-browser attacks – watch out for windows that aren’t!Simple but super-sneaky - use a picture of a browser, and convince people it's real...Leer másNaked...
U.S. Adds 2 More Chinese Telecom Firms to National Security Threat List
U.S. Adds 2 More Chinese Telecom Firms to National Security Threat ListThe U.S. Federal Communications Commission (FCC) has added Pacific Network Corp, along with its subsidiary...