A CISO’s critical recommendations for threat intelBy Pete Nicoletti, Check Point Field CISO, Americas If leveraged appropriately, cyber threat intelligence is a critical cyber security tool...
Month: August 2022
An encrypted ZIP file can have two correct passwords — here’s why
An encrypted ZIP file can have two correct passwords — here's whyPassword-protected ZIP archives are common means of compressing and sharing sets of files—from sensitive documents to...
58% of Organizations Surveyed Report that Third Parties and Suppliers Were the Target of a Cloud-Based Breach in 2021, Cloud Security Alliance and Proofpoint Study Reveals
58% of Organizations Surveyed Report that Third Parties and Suppliers Were the Target of a Cloud-Based Breach in 2021, Cloud Security Alliance and Proofpoint Study RevealsContenido...
How secure is your hybrid data center?
How secure is your hybrid data center?By Dave Gronner, Product Marketing Manager, Security Platforms, Check Point. As data centers evolve, so do the cyber attacks An...
Top 7 reasons to try out the CISO-as-a-Service model
Top 7 reasons to try out the CISO-as-a-Service modelEXECUTIVE SUMMARY: Dedicated security expertise, optimization, governance and innovation on-demand? Almost. For a subset of businesses, the CISO-as-a-Service...
CVE-2022-31656: critical auth bypass flaw in multiple VMware products
CVE-2022-31656: critical auth bypass flaw in multiple VMware productsVMware on Tuesday announced patches for several critical and high-severity vulnerabilities affecting VMware Workspace ONE Access, Identity Manager,...
Black Hat insights: Getting bombarded by multiple ransomware attacks has become commonplace
Black Hat insights: Getting bombarded by multiple ransomware attacks has become commonplaceThe top ransomware gangs have become so relentless that it’s not unusual for two or...
Cybersecurity Solutions Must Evolve, Says Netography CEO
Cybersecurity Solutions Must Evolve, Says Netography CEOJust as cyber criminals change tactics and strategy for more effectiveness, so must infosec pros and their organizations, according to...
State-Sponsored APTs Dangle Job Opps to Lure In Spy Victims
State-Sponsored APTs Dangle Job Opps to Lure In Spy VictimsAPTs continue to exploit the dynamic job market and the persistent phenomenon of remote working, as explored...
Black Hat Fireside Chat: MSSPs are well-positioned to help companies achieve cyber resiliency
Black Hat Fireside Chat: MSSPs are well-positioned to help companies achieve cyber resiliencyNetwork security is in dire straits. Security teams must defend an expanding attack surface,...
Patch Now: 2 Apple Zero-Days Exploited in Wild
Patch Now: 2 Apple Zero-Days Exploited in WildThe fact that the flaws enable remote code execution, exist across all major Apple OS technologies, and are being...
Black Hat Fireside Chat: Replacing VPNs with ZTNA that leverages WWII battlefield tactics
Black Hat Fireside Chat: Replacing VPNs with ZTNA that leverages WWII battlefield tacticsThe sunsetting of Virtual Private Networks is underway. Related: VPNs as a DIY tool...
NIST Weighs in on AI Risk
NIST Weighs in on AI RiskNIST is developing the AI Risk Management Framework and a companion playbook to help organizations navigate algorithmic bias and risk.Leer másDark...
Intel Adds New Circuit to Chips to Ward Off Motherboard Exploits
Intel Adds New Circuit to Chips to Ward Off Motherboard ExploitsThe countermeasure, which compares the time and voltage at which circuits are activated, is being implemented...
Banyan Recommends Phased Approach When Introducing Zero Trust
Banyan Recommends Phased Approach When Introducing Zero TrustBanyan Security’s Jayanth Gummaraju makes the case for why zero trust is superior to VPN technology.Leer másDark ReadingBanyan Security’s...
DeepSurface Adds Risk-Based Approach to Vulnerability Management
DeepSurface Adds Risk-Based Approach to Vulnerability ManagementDeepSurface’s Tim Morgan explains how network complexity and cloud computing have contributed to the challenge, and how automation can help.Leer...
The HEAT Is On, Says Menlo Security
The HEAT Is On, Says Menlo SecurityNeko Papez, senior manager, cybersecurity strategy for Menlo Security, helps customers understand if they’re vulnerable to highly evasive adaptive threats...
PIXM: Stopping Targeted Phishing Attacks With ‘Computer Vision’
PIXM: Stopping Targeted Phishing Attacks With 'Computer Vision'Chris Cleveland, founder of PIXM, talks about phishers’ evasive maneuvers and how organizations can tap Computer Vision to keep...
Mimecast: Mitigating Risk Across a Complex Threat Landscape
Mimecast: Mitigating Risk Across a Complex Threat LandscapeGarret O’Hara of Mimecast discusses how companies can bolster security of their Microsoft 365 and Google Workspace environments, since...
Encrypted Messaging Service Hack Exposes Phone Numbers
Encrypted Messaging Service Hack Exposes Phone Numbers Many people opt for encrypted messaging services because they like the additional layers of privacy they offer. They allow...
Heimdal® Is a Finalist at the Computing Security Awards 2022 in Eight Categories
Heimdal® Is a Finalist at the Computing Security Awards 2022 in Eight CategoriesWe are thrilled to announce that Heimdal®’s cybersecurity solutions were selected as finalists for...
Data breaches on gaming sites are becoming more common
Data breaches on gaming sites are becoming more commonWith a number of gaming sites falling victim to data breaches in July of this year, CS Hub...
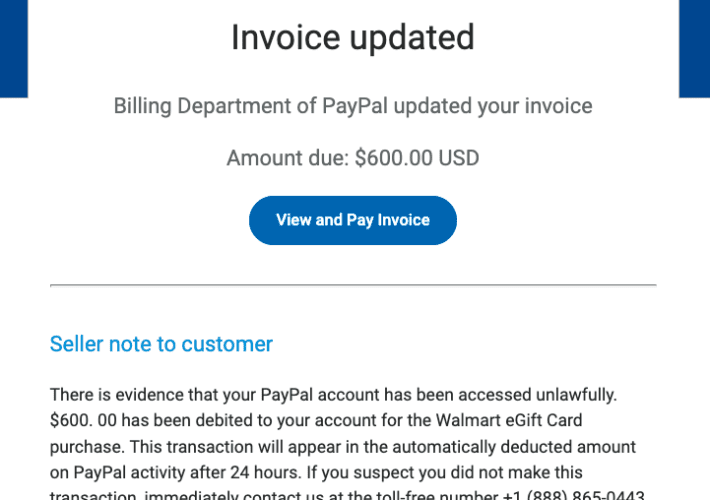
PayPal Phishing Scam Uses Invoices Sent Via PayPal
PayPal Phishing Scam Uses Invoices Sent Via PayPalScammers are using invoices sent through PayPal.com to trick recipients into calling a number to dispute a pending charge....
USB “Rubber Ducky” Attack Tool
USB “Rubber Ducky” Attack ToolThe USB Rubber Ducky is getting better and better. Already, previous versions of the Rubber Ducky could carry out attacks like creating...
Friday Squid Blogging: The Language of the Jumbo Flying Squid
Friday Squid Blogging: The Language of the Jumbo Flying SquidThe jumbo flying squid (Dosidicus gigas) uses its color-changing ability as a language: In 2020, however, marine...
BlackByte ransomware v2 is out with new extortion novelties
BlackByte ransomware v2 is out with new extortion noveltiesA new version of the BlackByte ransomware appeared in the threat landscape, version 2.0 uses extortion techniques similar to...
Entrust Allegedly Hit with LockBit Ransomware
Entrust Allegedly Hit with LockBit RansomwareThe LockBit ransomware group has declared that it was behind the American software company Entrust incident that occurred in June. At...
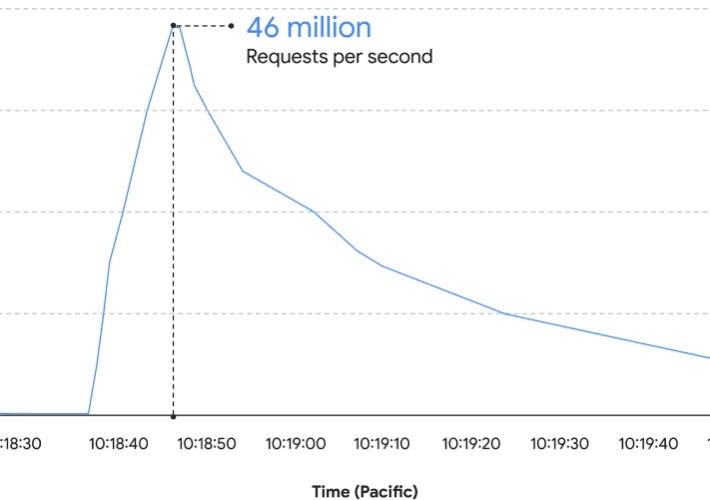
Google blocked the largest Layer 7 DDoS reported to date
Google blocked the largest Layer 7 DDoS reported to dateGoogle announced to have blocked the largest ever HTTPs DDoS attack, which reached 46 million requests per...
Safari 15.6.1 addresses a zero-day flaw actively exploited in the wild
Safari 15.6.1 addresses a zero-day flaw actively exploited in the wildApple released Safari 15.6.1 for macOS Big Sur and Catalina to address a zero-day vulnerability actively...
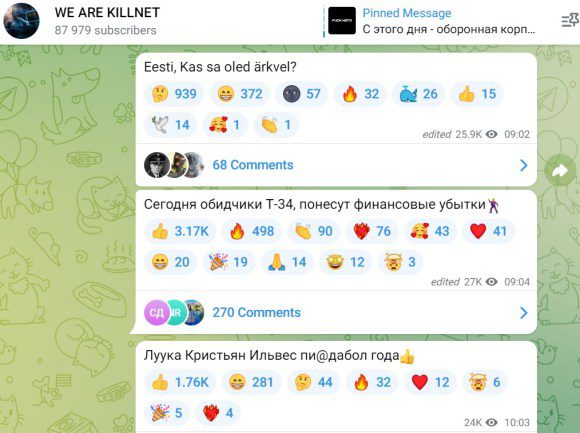
Estonia blocked cyberattacks claimed by Pro-Russia Killnet group
Estonia blocked cyberattacks claimed by Pro-Russia Killnet groupEstonia announced to have blocked a wave of cyber attacks conducted by Russian hackers against local institutions. Undersecretary for...