Armageddon APT aka UAC-0010 Uses GammaLoad and GammaSteel Malware in Targeted Cyber-Attacks on Ukraine With the outbreak of the global cyber war, the malicious activity of...
Day: August 13, 2022
Ransomware attack blamed for closure of all 7-Eleven stores in Denmark
Ransomware attack blamed for closure of all 7-Eleven stores in DenmarkRansomware is to blame for the closure of all 175 7-Eleven stores in Denmark on Monday....
A Taxonomy of Access Control
A Taxonomy of Access ControlMy personal definition of a brilliant idea is one that is immediately obvious once it’s explained, but no one has thought of...
Twitter Exposes Personal Information for 5.4 Million Accounts
Twitter Exposes Personal Information for 5.4 Million AccountsTwitter accidentally exposed the personal information—including phone numbers and email addresses—for 5.4 million accounts. And someone was trying to...
Friday Squid Blogging: SQUID Acronym for Making Conscious Choices
Friday Squid Blogging: SQUID Acronym for Making Conscious ChoicesI think the U is forced: SQUID consists of five steps: Stop, Question, Understand, Imagine, and Decide. As...
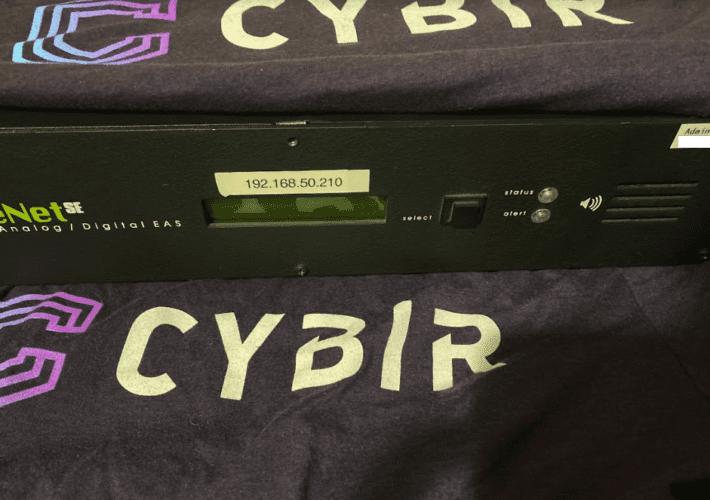
Sounding the Alarm on Emergency Alert System Flaws
Sounding the Alarm on Emergency Alert System FlawsThe Department of Homeland Security (DHS) is urging states and localities to beef up security around proprietary devices that...
Back to School: Tech Savvy vs. Cyber Savvy
Back to School: Tech Savvy vs. Cyber Savvy The first day of school is right around the corner. The whole family is gearing up for a...
Identity and Access Management at NIST: A Rich History and Dynamic Future
Identity and Access Management at NIST: A Rich History and Dynamic FutureDigital identity for access control is a fundamental and critical cybersecurity capability that ensures the...
Microsoft: We Don’t Want to Zero-Day Our Customers
Microsoft: We Don't Want to Zero-Day Our CustomersThe head of Microsoft's Security Response Center defends keeping its initial vulnerability disclosures sparse — it is, she says,...
Chinese hackers backdoor chat app with new Linux, macOS malware
Chinese hackers backdoor chat app with new Linux, macOS malwareVersions of a cross-platform instant messenger application focused on the Chinese market known as 'MiMi' have been...
Best penetration testing tools: 2022 buyer’s guide
Best penetration testing tools: 2022 buyer’s guideSecurity professionals need penetration testing tools to understand the security posture of every software environment. Check out our list of...
How to Clear Security Obstacles and Achieve Cloud Nirvana
How to Clear Security Obstacles and Achieve Cloud NirvanaBack-end complexity of cloud computing means there's plenty of potential for security problems. Here's how to get a...
Novel Ransomware Comes to the Sophisticated SOVA Android Banking Trojan
Novel Ransomware Comes to the Sophisticated SOVA Android Banking TrojanUnusually, SOVA, which targets US users, now allows lateral movement for deeper data access. Version 5 adds...
Software Supply Chain Chalks Up a Security Win With New Crypto Effort
Software Supply Chain Chalks Up a Security Win With New Crypto EffortGitHub, the owner of the Node Package Manager (npm), proposes cryptographically linking source code and...
Palo Alto bug used for DDoS attacks and there’s no fix yet
Palo Alto bug used for DDoS attacks and there's no fix yetThere goes the weekend... A high-severity Palo Alto Networks denial-of-service (DoS) vulnerability has been exploited...
Latin America: A region of challenges and opportunities
Latin America: A region of challenges and opportunitiesFrancisco Robayo is a cyber security expert with 15 years of experience in the sector and more than 20...